Why are “complex factory networks” dangerous?
As factory networks continue to add lines and upgrade equipment, the number of devices and communications increases, and they naturally become more complex over time. By the time you realize it, it's easy to lose sight of the big picture: what's connected to what? The more complex the network, the greater the risks in terms of both operation and safety. For example, it's easy to lose track of the scope of a problem, with abnormal communications from one device affecting other lines, or a configuration change unexpectedly affecting other devices.
Furthermore, if the network structure remains unclear,
- It takes time to isolate the cause of the problem
- "We have no choice but to be cautious" about updates and adding equipment.
- Only certain people in charge understand the whole picture
Concerns about daily operations such as these continue to grow. Furthermore, when networks are operated as a single, wide network with ambiguous boundaries, there is a greater chance that anomalies such as communication problems or unauthorized access will spread throughout the entire factory. This type of complexity naturally arises in factory operations, but if left unchecked, it can lead to an "uncontrollable range of impact," increasing operational burdens and security risks.
The idea of creating a "safe floor plan" for factories: What is the Network Concept?
In order to organize complex factory networks and minimize the impact of problems and attacks, a common design philosophy is needed to review the structure itself. The Network Concept has been compiled as a reference design for exactly this purpose. This approach is based on the Secure Reference Architecture published by Siemens, and the latest Network Concept V2.0 clearly incorporates the idea of Zero Trust (meaning that communication is generally not permitted, and only necessary communications are permitted).
The core idea of the Network Concept is comprised of three main pillars.
Divide the factory into "cells" (L3 division)
The idea is to divide a factory into small rooms (cells) based on lines or equipment, rather than operating it as one large network.
- Problems that occur in one cell are contained within that cell
- The structure is well-organized, making it easy to understand the communication path.
- The scope of impact of fault isolation and update work becomes clear
The expression "safe floor plan" clearly illustrates the concept of cell division.
"Allow only necessary communications" at zone boundaries
The idea of Zero Trust is adopted at the boundaries between cells, or zone boundaries. Firewalls and other control points are set up at the boundaries, explicitly permitting only necessary communications and blocking all others. This is a distinctive design of the Network Concept.
This means:
- Eliminate unnecessary communication between cells
- Prevents abnormal communication from spreading to other cells
- Stops lateral expansion even if an attack penetrates
This ensures structural strength.
Securely connect IT and OT via a DMZ (demilitarized zone separated by a firewall)
If the factory network (OT) and the company network (IT) are directly connected, there is a risk that any problems or attacks that occur on either network will spread to the other. For this reason, a DMZ (a buffer zone separated by a firewall) is set up between the two networks to enable safe data exchange.
This means:
- Avoid direct OT-IT connections
- It will be easier to prevent outsiders from reaching the factory.
- Data can be updated and managed safely
The following effects can be achieved.
The three concepts introduced so far - "cell division," "minimum permitted communication at the boundary," and "DMZ for separating IT and OT" - are organized into the overall architecture of the Network Concept. The diagram below shows the "overall structure" when these concepts are deployed across the entire factory network.
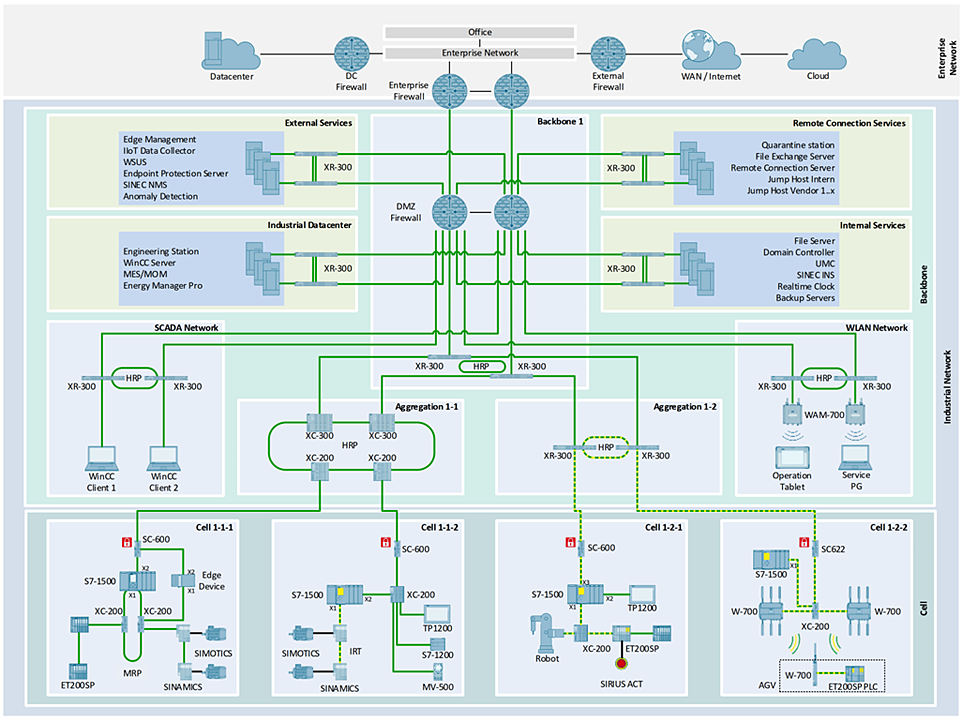
Source: Siemens AG – “Network Concept for Factory Automation V1.0”
Multi-layered defense to "protect the structure": The role of defense in depth
Network Concept is not simply a design method for organizing networks in an easy-to-understand manner. In fact, it is also a way to put Siemens' industrial cybersecurity strategy, Defense in Depth, into practice within factory networks. Defense in Depth is a concept based on IEC 62443, and its basic concept is to "protect a factory not with one large wall, but with multiple layers."
Siemens explains this defense in depth by dividing it into three main layers:
Plant Security (Physical security at factories and worksites)
The first layer is security to protect the actual space of the factory itself, which targets "people" and "places" rather than networks.
- Lock the control room and the panel to prevent unauthorized opening.
- Controlling access to factory areas to prevent unauthorized persons from entering
- Cameras and sensors monitor suspicious activity and intrusions
- Establish operational rules such as who can touch which equipment and what procedures should be followed.
This layer ensures that on-site equipment cannot be directly accessed in the first place through measures such as these. No matter how much the network is strengthened, security cannot be achieved if anyone can open the control panel and operate the PLC directly. In that sense, Plant Security is the "outermost layer of defense" that serves as a prerequisite for the other layers.
Network Security
The second layer is directly related to the Network Concept, the theme of this article. What is protected here are the communication routes within the factory and between the factory and the internal network. For example, the following measures are taken in this layer:
- Divide the factory into zones/cells Segmentation
- Establish a demilitarized zone (DMZ) between IT and OT to avoid direct connections
- Place firewalls and ACLs at the zone boundaries to allow only permitted communications.
- Use VPNs and encrypted communications to provide only secure routes for remote connections.
All of these are mechanisms aimed at preventing attackers and abnormal communications from moving laterally freely within the factory network. The structures suggested by the Network Concept, such as dividing into cells, passing only necessary communications at the boundary, and establishing a DMZ, can be said to embody how to design this Network Security layer.
System Integrity (security that protects the integrity of devices and systems)
The third layer is security for the control devices and systems inside the network itself, such as PLCs, drives, HMIs, and industrial PCs. This includes the following measures:
- User authentication and authority management for each device
- Encryption of communications and configuration data
- Firmware and settings tamper-proof function
- Log and audit system that records important operations and events
- Appropriate application management of patches and updates
This allows the device to act as a last resort, ensuring that even if the outer defenses of the network are breached, the device itself cannot be easily taken over.
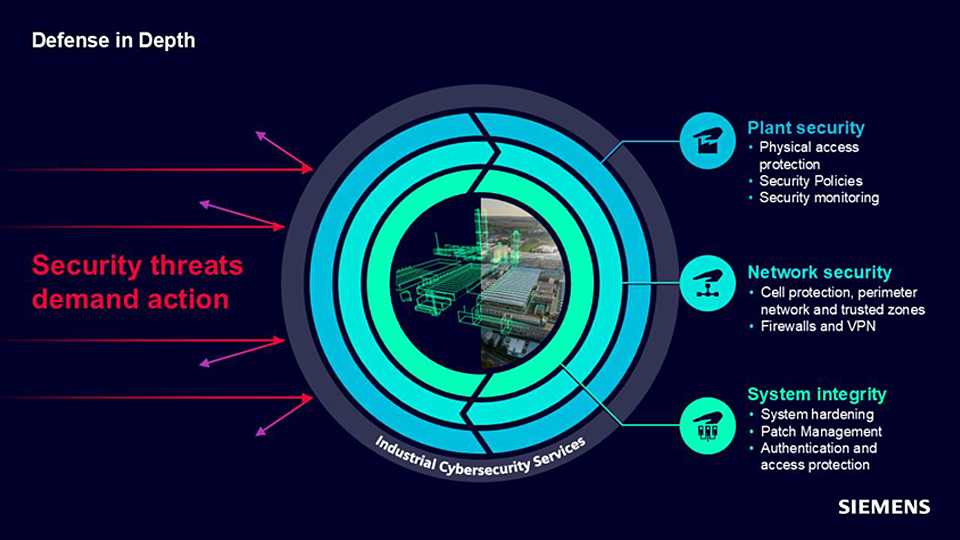
Source: Siemens data
The diagram above is a conceptual diagram visualizing the three-layer structure of Defense in Depth. Defense in Depth is a concept that is realized by combining these three layers.
- Preventing unauthorized entry into the "location" known as the factory
- Controlling connections within the factory and limiting the scope of influence
- However, in case of a breach, protect the "device itself"
By layering these defenses, we can create a factory that is difficult to infiltrate from the outside, difficult to spread even if an attack does infiltrate, and ultimately can stop the attack with equipment. Within this, the Network Concept is the framework for realizing the Network Security layer, and by combining it with SINEC, SCALANCE, and IEC 62443-compliant FA devices, it is possible to implement all three layers of Defense in Depth in a balanced manner.
What is needed to make the design concept "work in the field"?
The Network Concept and Defense in Depth are design concepts that organize factory networks into a "safe floor plan" and provide multiple layers of protection. To put this into practice in an actual factory, it is necessary to appropriately combine the products and mechanisms that support the three layers of Defense in Depth.
Here, we will focus on the Network Security and System Integrity layers and organize the representative product categories that support their implementation.
The "operational platform" that supports all three layers: SINEC NMS
First, after designing the three layers, SINEC NMS (Integrated Network Management) serves as the foundation for maintaining that state over the long term.
- Visualization of network topology and communication status
- Network device configuration and firmware (FW) management
- Centralized distribution of firewall/ACL settings to SCALANCE
- Update and change management
These functions allow the system to constantly understand the current state of the factory network and act as an operational foundation for maintaining the structure as designed. In terms of the Defense in Depth diagram, it is positioned to support the operation and monitoring layer that surrounds the "outside" of the three layers.
Implementing the Network Security Layer (the core of the Network Concept): SCALANCE
The SCALANCE series (industrial network equipment) is at the heart of realizing the "secure floor plan" outlined in the Network Concept, including cell division, boundary control, and DMZ, as a physical network.
- L2/L3 Switch
- Industrial Firewall
- NAT/Routing
- Redundancy (MRP / PRP / HSR)
- Communication control at zone/cell boundaries
These products fulfill the roles described above and can be said to embody the structure of the Network Security layer itself, such as "separating cells," "passing only necessary communications at the boundary," and "connecting IT/OT via DMZ."
Implementing the System Integrity Layer (Device-Level Protection): IEC62443-compliant Devices
Even if the outer network defenses are breached, the System Integrity layer is the last line of defense to protect the equipment itself, and this is supported by IEC62443-compliant PLCs, drives, and other FA devices.
- User authentication and authorization management
- Encryption of communication and setting data
- Prevents tampering with settings and firmware
- Operation and event logging
- Patch/Update Management
These functions provide a layer of risk reduction at the device level, even if countermeasures on the network side are circumvented.
In this way, by viewing the design concept (Network Concept × Defense in Depth) and the product group that supports it as a set, it becomes possible to visualize the desired operational state - a factory that is easy to manage, easy to update, and resistant to attacks - as a specific configuration.
What will change if we incorporate the idea of floor plans into the design concept of factory networks?
In complex factory networks, there are still communications that are not necessarily required. PLC or HMI It is possible to access it from multiple routes,“It doesn't matter where anything comes from”In this state, if a failure or attack occurs, the impact is likely to spread widely, and it takes time to identify the cause, leading to ongoing concerns about daily operations.
Network Concept and Defense in Depth Combined“Floor plan ideas”With this in place, the structure changes to:
Backdoor communications are streamlined, making lateral movement less likely (Network Security layer)
By dividing the factory network into cells and allowing only necessary communications at the boundaries, the "backdoor communications" that previously existed can be significantly reduced.
|
Example: 250 unnecessary routes → 50 necessary routes (approximately 80% reduction)
|
As a result, even if an intrusion or abnormal communication does occur, the structure makes it difficult for it to spread laterally.
Cell division reduces the impact of failures and attacks (Network Security layer)
By dividing the entire factory into cells, even if a failure occurs, the impact is more likely to be contained within that cell.
|
Example: The affected area is reduced by approximately 95% compared to the previous case.
|
This significantly speeds up troubleshooting and reduces the workload required for recovery.
The PLC/Drive itself becomes stronger, and the final stronghold is established (System Integrity layer)
By incorporating the "security functions of the device itself" in accordance with IEC62443, such as authentication, encryption, tamper prevention, and log management, even if the network-side countermeasures are breached,
- Unauthorized access
- Configuration tampering
- Unauthorized manipulation
This will enable risks such as these to be reduced at the equipment level.
Physical access is also controlled, reducing on-site risks (Plant Security layer)
By establishing mechanisms to reduce the risk of physical intrusion, such as locks, access control, and surveillance cameras,
- The device is opened and operated without permission
- Unauthorized items such as USBs are brought in
This also reduces "real-world vulnerabilities" such as:
Visualization and operational improvements make factories less susceptible to downtime (operational infrastructure)
SINEC NMS visualizes devices and communications and manages configurations,
- You can immediately see what is abnormal
- Configuration consistency is easily maintained
- Fast recovery
This will also enhance operational aspects.
By combining these changes, the Network Concept × Defense in Depth structure will lead to a "factory network that continues to operate safely" that is "difficult to enter," "difficult to spread," "difficult to stop," and "easy to recover."
Four steps you need to understand to make your factory easy to manage, update, and resilient to attacks
When incorporating the Network Concept and Defense in Depth into a factory, it is not necessary to first determine detailed work procedures. Rather, what is important is to have four perspectives that determine the order in which to think about things to create a safe structure.
This is where the Network Concept comes into play.
By SINEC NMS
The Network Concept and Defense in Depth are the foundations for "functioning in daily operations."
These four steps are not a specific procedure manual, but rather an essential perspective for considering a safe factory network floor plan.
Summary: Network Concept × Defense in Depth for "an easy-to-manage factory that is resistant to attacks"
By changing the factory network to an "organized, easily defendable structure," both daily operations and security measures become much easier to handle. Network Concept x Defense in Depth is a"set of ways of thinking"for that purpose. I hope that the contents of this article will help you realize, even just a little, that "this seems to apply to my factory," or "I now have an idea of where I should start reviewing."
If you have any questions or would like more specific information, please feel free to contact us. We will work with you to support you in creating a factory that is easy to manage and resistant to attacks.
Inquiry
If you have any questions or concerns about this article, please contact us using the form below.
Go to Siemens OT (Operational Technology) product page
If you are interested in Siemens OT (Operational Technology) products, please visit the following page.