Conducting research into trends in cyber attacks targeting Japan and countermeasures,
Returning the knowledge gained to various social activities

Cyberattacks, which invade the systems of government agencies and private companies to steal confidential information such as intellectual property and personal information, are becoming more sophisticated and intensifying, and the damage caused by such attacks has become a major social issue. "We want to do something about this situation," "We want to make cyberspace safe for everyone to use." With this mission in mind, Macnica established the Security Research Center in 2013 as a purely research institute independent of its business divisions. The center conducts research into trends in cyberattacks targeting Japan and countermeasure solutions, and feeds back the knowledge it gains into various social activities.
Characteristics of the activity
Research into "threats to Japan" that are not just overseas
In the case of intelligence attacks, the situation varies greatly from country to country in terms of who is attacking and what type of attack is being received. Therefore, in order to deal with attacks landing on Japan from overseas, it is necessary to investigate and analyze not only cases of damage outside of Japan, but also the damage situation within Japan. However, information disseminated from the United States and Israel, which are advanced security nations and produce many countermeasure solutions, does not always accurately capture and reflect trends within Japan. Therefore, the Security Research Center is focusing on investigating and analyzing cyber attacks that occur within Japan.
Research into current real-world threats, not just basic security research or armchair theory
While supporting many customers, Macnica obtains and analyzes a large amount of information on attacks that Japanese companies have actually suffered. In the security industry, attention is sometimes focused on theoretical threats and various buzzwords, but the Security Research Center, from among the various pieces of information that are generated every day, places emphasis on whether or not something is actually being used in an attack, or has the potential to be used, and investigates and disseminates information on "what measures customers should truly take now," without being misled by empty theories or trends.
Investigating not only threats but also countermeasure solutions and methods
The Security Research Center is also researching the necessary countermeasure solutions and methods, with an eye on future threat trends. Macnica has been able to discover cutting-edge security products with outstanding functions from around the world and quickly provide them to the Japanese market, with the knowledge and experience of the Security Research Center at the forefront.
Research Area
While focusing on three areas in particular - targeted attacks by nation-state groups aimed at espionage and information theft, Attack Surface Management to discover insufficiently managed assets exposed to the public, and security related to AI and LLM - we also research and gain insights into a variety of other technical fields.
- Focus Areas
- Targeted attack trends
- Attack Surface Management
- AI/LLM Security
- Other initiatives
- Email security (phishing, email fraud, etc.)
- Red team (intrusion and breach techniques)
- web application security
- Ransomware Trends
- IoT・OT
- Vulnerability management and threat trends
- Web 3.0 related
- Incident response
- Mass Cybercrime (Smishing)
External Activities
In order to give back the results of our research to society, we are currently participating in well-known security conferences in the industry, writing articles, and working with government agencies and public institutions. As for security conferences, we continually submit papers to the Call for Papers (CFP), which are reviewed for novelty, originality, and value of the information, and we continue to present papers every year on selected papers. The presentations are the results of world-class research, and the contents of our reports and other materials are frequently referenced and cited by well-known security vendors, public institutions, and media.
- international conference
- Black Hat Arsenal USA, Asia, MEA
- HITCON
- Mandiant Cyber Defense Summit
- Bsides LV, Brisbane, Austin
- Virus Bulletin
- Security Analyst Summit
- Domestic conference
- JSAC
- BSides Tokyo
- (ISC)² Japan Chapter Annual Conference
- Sasakawa Peace Foundation Cyber Security Seminar
- Information Security Workshop in Echigo-Yuzawa
- Shirahama Symposium
- Other social activities
- Security Camp National Convention Lecturer
- Global Security Camp Lecturer
- Security Advisor for Government Agencies
- FY2021 Multinational Cyber Defense Competition
- Research Committee Member, 21st Century Public Policy Institute, Japan Business Federation
- Security Community Hamasec Operated
- MINI Hardening Management
- CODE BLUE Cyber TAMAGO Management
- Writing Activities
- Security Research Center Blog
- Incident Response, 3rd Edition, Supervised Translation
- White Paper Publication


member
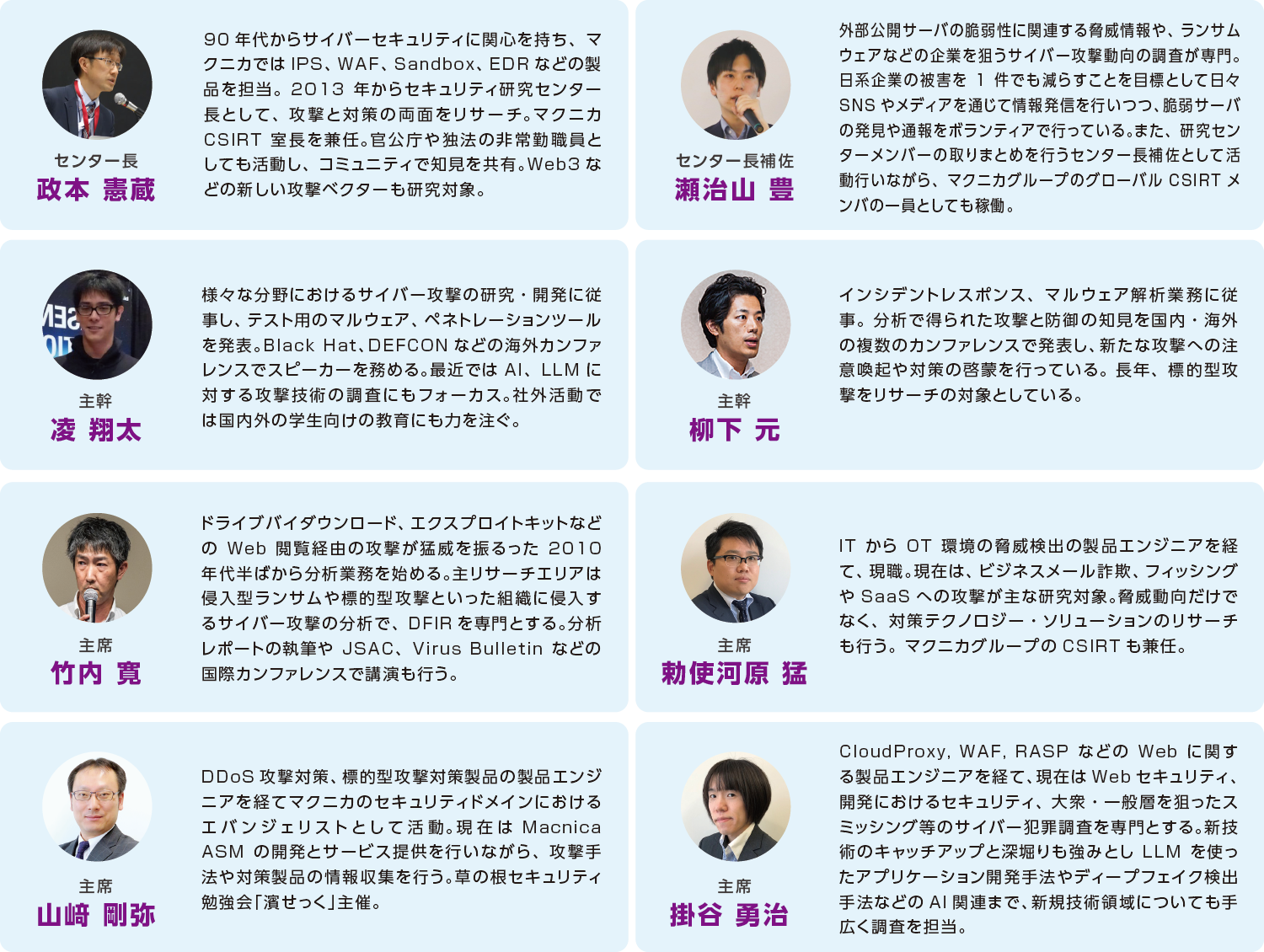
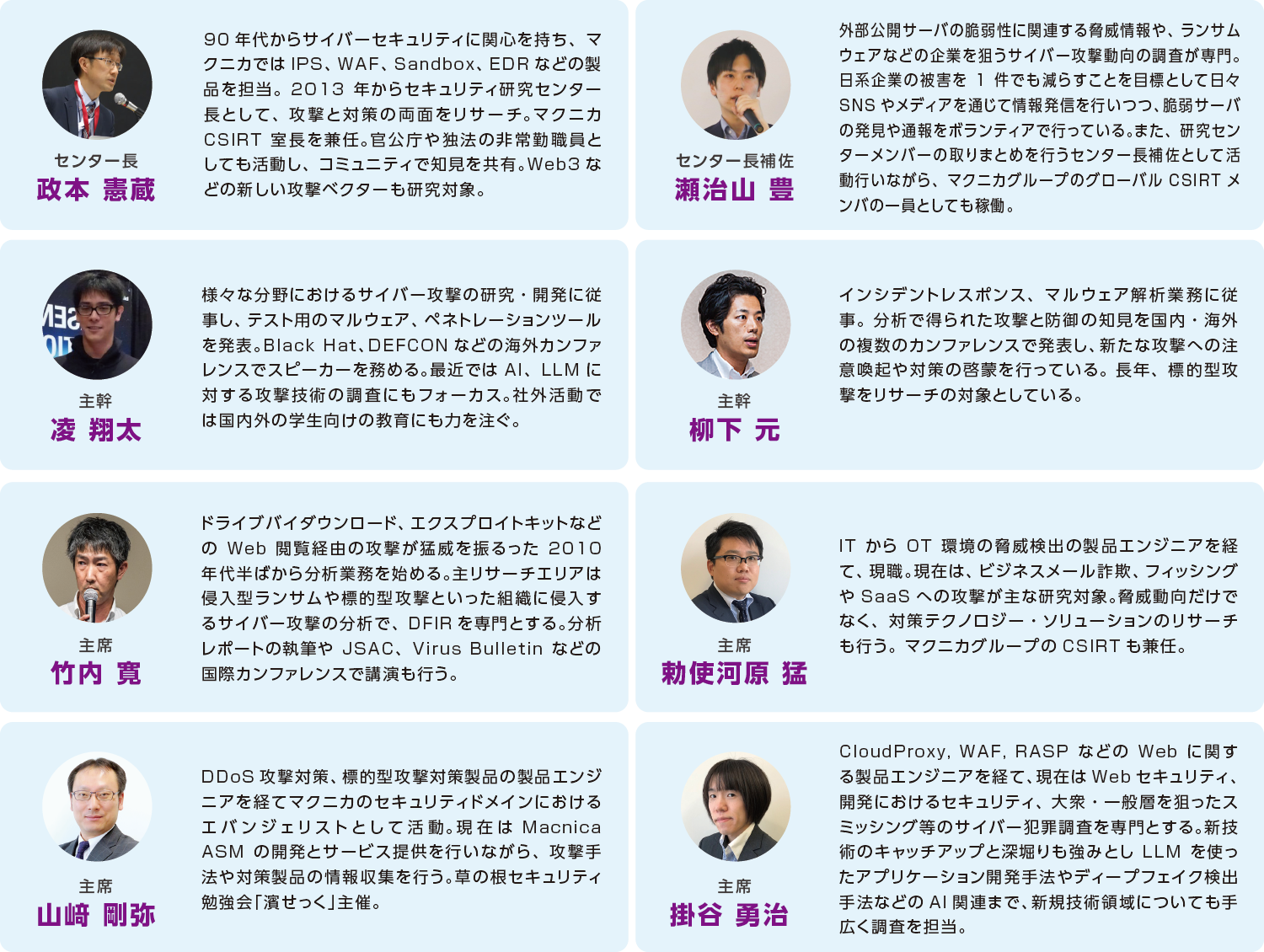
Members' Areas of Expertise


Security Report
Security Research Center Blog
We are uploading Macnica own information regarding security.
Security Related Information
Also check this