What is threat analysis?
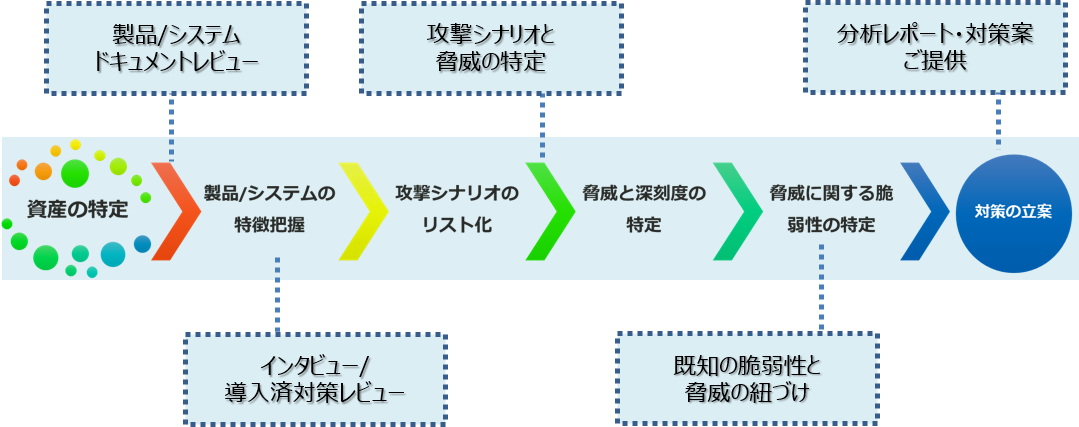
The threat analysis provided by Spirent reviews the specifications and other documents of the customer's product, and if necessary, conducts interviews and on-site visits, etc., to grasp the outline of the assets to be protected and the environment in which the target product is placed. Based on this information, we list attackers, attack scenarios, threats, and vulnerabilities, rank them according to the degree of impact if left unattended, and propose countermeasures.
Why is Threat Analysis Necessary?
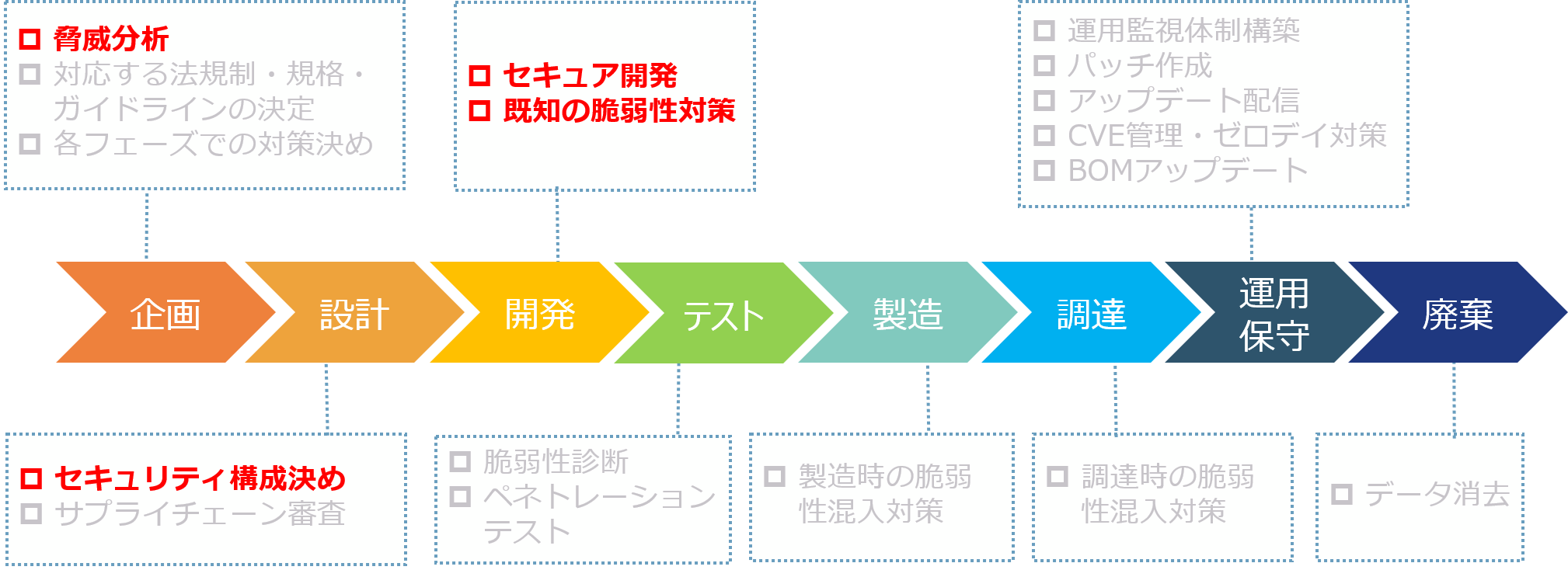
In recent years, security regulations and standards for IoT devices have begun to be developed, and at development sites, threat analysis is required as a security examination method in the upstream development process. So why is threat analysis needed? I will explain why.
Know your product's security risks
In order to correctly grasp what kind of security risks exist in the device to be designed from now on, it is effective to conduct a threat analysis at the "planning" stage, which is the upstream stage of device development. By understanding the risks in general, you can classify them into those that require countermeasures and those that are acceptable.
Consider the necessary security measures for your own equipment
Security measures tend to start with security functions such as encryption and tampering detection, but in reality, it is important to implement measures to deal with individual threats. Analysis in the upstream development has the effect of preventing the overlooking of essential measures and preventing the implementation of unnecessary measures.
Justify security measures
Security measures that are implemented without evidence lack persuasiveness to customers. If it is a countermeasure derived from the implementation of threat analysis and analysis results, it will be possible to appeal to the outside world.
Benefits of performing a threat analysis
As mentioned above, threat analysis has become essential even at the site of device development. This is a very difficult situation to implement. Here, we describe the benefits that can be obtained by teaming up with a security testing vendor to conduct a threat analysis.
Realize analysis without omissions
Since the knowledge of the consultant is combined with the threat/vulnerability database, a highly comprehensive threat analysis can be achieved.
Can determine appropriate security measures
We have the knowledge to derive appropriate countermeasures against threats, so we can support the implementation of optimal security countermeasures that development sites most require.
You can accumulate knowledge of security related to your own equipment
Analysis results are provided as a report. Since the analyzes are conducted for the environment normally assumed for the equipment to be developed, the report can be used as a reference when developing other models and successor models.
Threat analysis execution flow
As mentioned above, threat analysis must be conducted in a thorough manner. At Spirent, we provide reliable analysis results by proceeding according to the following flow based on the reliable knowledge of our consultants.
Inquiry
If you have any questions or inquiries, please contact us below.
Spirent manufacturer information Top
If you want to return to Spirent manufacturer information top page, please click below.
