Introduction
In recent years, security incidents have been increasing and diversifying due to the increase in data volume and the expansion of cloud utilization. Furthermore, the decentralization and increased complexity of protection caused by innovations in IT infrastructure such as cloud and SaaS have exposed data to new threats. As the key to solving these problems, the security technology of "data protection" is attracting attention once again.
Here, we will explain the basics of data protection using the keyword "key management (KMS)," which is one of the encryption technologies.
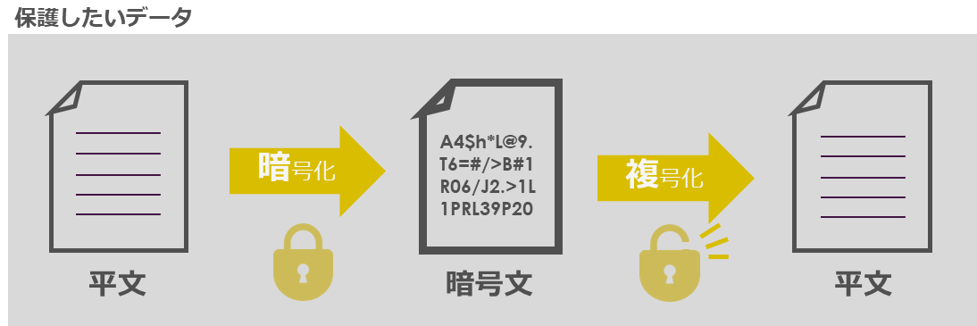
Basics 1: What is data encryption?
Data encryption is the primary process for protecting digital information by converting the data into a string of meaningless characters (ciphertext) that make it unreadable to others.
Ciphertext is a meaningless string of characters and cannot be deciphered. Therefore, even if information is leaked, as long as the data is encrypted, there will be no substantial damage.
Basics 2: Why is encryption attracting attention now?
Traditionally, perimeter defense (a security method that protects the infrastructure itself) was adopted, but in recent years, incidents have been increasing due to the shift to the cloud.
Below are some of the new security risks that have emerged in recent years.
●Background 1: As data storage has shifted from on-premise to the cloud and SaaS, there are no longer clear boundaries within the infrastructure, creating a multitude of intrusion routes for external users.
●Background 2: There are malicious users even within the boundaries of infrastructure, and the number of data leaks due to internal fraud is increasing.
In other words, encryption is a noteworthy technology that ultimately makes it possible to protect the very data that we want to protect.
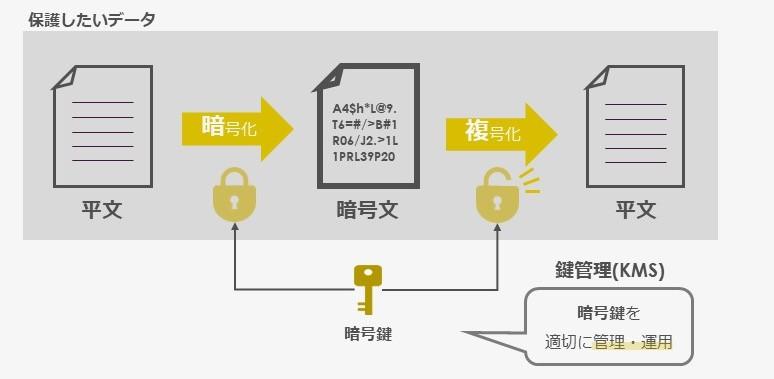
Basics 3: The most important aspect: What is “Key Management (KMS)”?
An "encryption key" is used to encrypt data (convert it into meaningless characters) and decrypt it (return it to the original readable data). In order to eliminate the risk of data leakage, it is necessary to properly manage and operate the encryption key, and it is important to consider how to properly authenticate and manage the "key management (KMS)" to decrypt data by only authenticating trusted viewers.
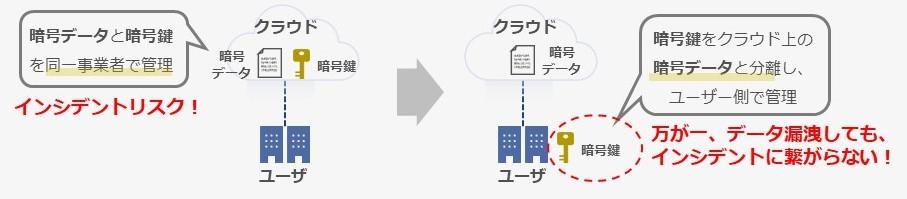
Summary: Cloud-based Key Management (KMS)
Data stored in the cloud is often encrypted, but because both the encrypted data and the encryption keys are managed by the cloud service provider, there is a risk that the data and the encryption keys may be leaked together, which could lead to an incident.
In addition, did you know that AWS’s shared responsibility model states that “users are responsible for encrypting their own data”? This means that users are responsible for ensuring the security of their data, especially when it contains confidential information.
In other words, the security measures that are required these days are, in principle, to separate the keys and encrypted data, and to store and manage them appropriately on the user's side, even in cases where the encrypted data is managed by the cloud provider.
Key management solutions necessary in the cloud era
Fortanix offers a cloud-offloaded, centralized, user-managed Data Security Manager (DSM) key management solution, providing simpler and more robust protection of encrypted data.
We are also offering a free on-demand seminar for those who would like to learn more.
\On-demand seminar "Current zero trust measures are not enough! The importance of "data protection""/
Inquiry
If you have any other requests or questions, please contact us using the contact button below.
Fortanix Manufacturer Information Top
If you want to return to Fortanix Manufacturer Information Top, please click below.
