This page explains what WP.29 is, details about related regulations UN-R155 and UN-R156, and how to implement them, and also introduces specific solutions from ETAS, a company that handles Macnica products.
table of contents
What is WP.29?
WP.29 is a framework for international automotive regulations established by the United Nations Economic Commission for Europe (UNECE). As automobiles have become increasingly dependent on software in recent years, legal regulations regarding cybersecurity and software updates have been strengthened, leading to the introduction of new regulations UN-R155 (CSMS) and UN-R156 (SUMS).
Additionally, within Japan, the Ministry of Land, Infrastructure, Transport and Tourism has incorporated these regulations into its vehicle type approval system, establishing implementation and audit requirements for vehicle manufacturers,requiring them to implement measures across four different areasto address these risks.
- Managing vehicle cybersecurity
- Vehicle protection by design to mitigate risks along the value chain
- Detect and respond to security incidents across your fleet
- Clarifying legal compliance of vehicle software by providing safe and secure software updates and ensuring vehicle safety is not compromised
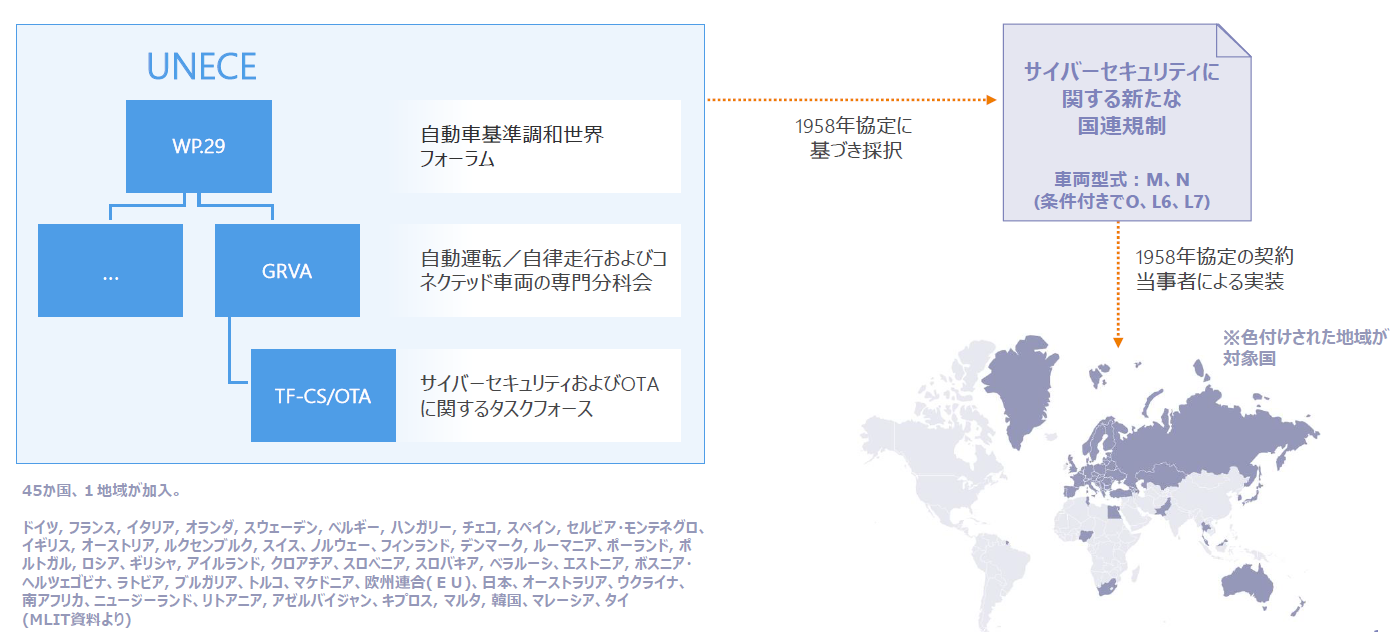
WP.29 Structure and requirements of the legislation
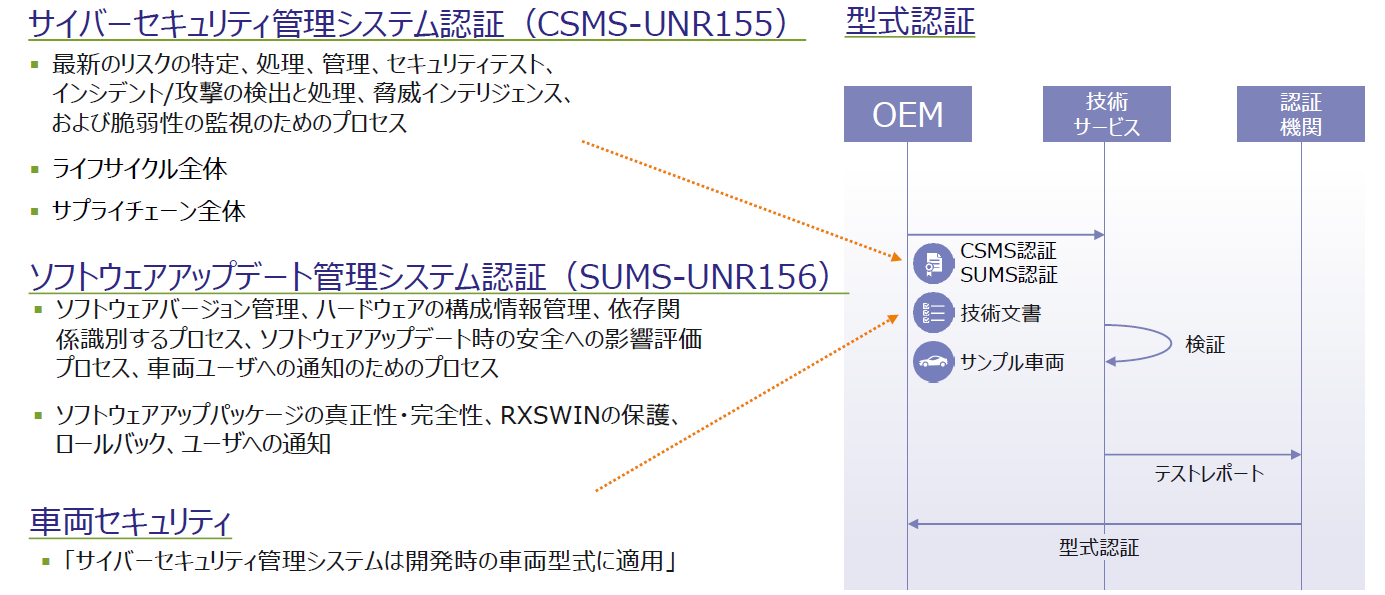
At the beginning, we mentioned UN-R155 (Cybersecurity Management System: CSMS) and UN-R156 (Software Update Management System: SUMS), which are essential requirements for vehicle manufacturers and suppliers to obtain type approval.
This section provides a practical explanation of the legal framework of WP. 29 and the key points of the structure, technology, and operations required by CSMS and SUMS, with the aim of helping you grasp the overall picture of compliance with the regulations and proceed with preparations for implementation.
UN-R155: Cybersecurity Management Systems (CSMS)
UN-R155 is an international regulation for systematically managing cybersecurity measures for automobiles. In recent years, vehicles have become increasingly connected to the Internet and external devices, increasing the risk of cyberattacks. CSMS requires "how to assess these risks and what kind of system to use to manage them."
| Threat Analysis (TARA) |
Analysis of threats to vehicle functions and communication paths(TARA: Threat Analysis and Risk Assessment). |
| Defining security requirements | The development department, quality control department, IT department, etc. work together to set up security gates in the development process. |
| Audits and Continuous Improvement | Establishment of the CSMS PDCA cycle for development (design stage), production (manufacturing stage), and operation (post-market release). |
UN-R156: Software Update Management System (SUMS)
UN-R156 is a regulation for the safe and reliable management of vehicle software updates. Modern vehicles require software updates even after they have been driven, so it is important to maintain update history and ensure safety.
| Management Structure and Record-Keeping | Record and track which vehicles have had software updates and when. |
| OTA update safety | We have created a system to encrypt communications and prevent tampering for OTA (Over-the-Air), which refers to software updates via wireless communication. |
| RxSWIN Management |
RxSWIN (Software Identification Number) is a number that uniquely identifies each software version.Update integrity and |
As such, UN-R155 and UN-R156 are regulations that focus on "security management" and "update management," respectively, and establishing systems for both is essential to comply with WP.29.
The following section describes the specific implementation and requirements.
How to Implement a Cybersecurity Management System (CSMS)
Below we will introduce specific methods for implementing CSMS.
Threat Analysis (TARA)
TARA is an abbreviation for Threat Analysis and Risk Assessment, and is a process of identifying cyber threats that exist based on vehicle usage scenarios and assessing the risks associated with them.
| Specific implementation example: |
|
Identify situations in which a moving vehicle communicates with the outside world (e.g., V2X communication, OTA updates). |
|
Threats such as eavesdropping, tampering, and spoofing are listed for each communication route. |
|
Each threat is scored based on its likelihood of occurrence and impact, and priorities are determined. |
| Specific examples of measures: |
| Implementing encrypted communications, authentication mechanisms, and firewalls. |
Related solutions
Defining security requirements
It is necessary to explicitly include security measures at each stage of the development process, which will enable early detection of design errors and vulnerabilities.
| Specific implementation example: | |
| Requirements definition phase: | Define security requirements in parallel with functional requirements (e.g., ECUs must have secure boot). |
| Design phase: | Install security gates and conduct design reviews to check whether threat countermeasures are in place. |
| Implementation phase: | Use cryptographic libraries and employ secure communication protocols. |
| Testing phase: | Conduct penetration testing and fuzz testing. |
Related solutions
Audits and continuous improvement (PDCA cycle)
A CSMS is not something that can be built once and then left alone; it must be continually improved. By implementing the PDCA (Plan-Do-Check-Act) cycle, it is possible to maintain and improve security levels.
| Specific implementation example: | |
| Plan: | Developing security policies and updating risk assessments. |
| Do: | Implementing countermeasures (e.g., software updates, vulnerability fixes). |
| Check: | Conducting audits and reviews to evaluate the response status when an incident occurs. |
| Act: | Implementing improvement measures and reviewing response policies to new threats. |
| Operation example: |
|
CSMS review meetings are held every six months to update risk assessments and countermeasure status. |
|
When an incident occurs, the cause is analyzed and measures to prevent recurrence are reflected in the CSMS. |
How to implement a Software Update Management System (SUMS)
Below we will introduce specific methods for implementing SUMS.
Management Structure and Record-Keeping
SUMS requires the establishment of a system that can record and track which software was updated for which vehicle, when, etc. This is the basis for type approval and compliance with regulations, and is essential for ensuring traceability.
| Specific implementation example: |
|
We have created an update management flow that corresponds to the vehicle life cycle (planning, design, development, production, market, and disposal). |
|
RxSWIN (software identification number) for each ECU is centrally managed and update history is recorded. |
|
After the update is completed, the update date and time, target ECU, RxSWIN, version, reason for update, etc. are automatically registered in the record-keeping system. |
OTA update safety
OTA (Over-the-Air) updates are a method of updating software wirelessly. Security measures such as encryption of communications, prevention of tampering, signature verification, and recovery functions are essential.
| Specific implementation example: |
|
Encryption technologies such as TLS are introduced into communication routes. |
|
An electronic signature is added to the update package and verified on the ECU side. |
|
Implemented rollback function in case of update failure (A/B bank configuration). |
RxSWIN Management
The RxSWIN (Rx Software Identification Number) is a number that uniquely identifies each software version. Accurate management of this number ensures the integrity and traceability of updates.
| Specific implementation example: |
|
RxSWIN is assigned to each ECU to determine whether changes are necessary when updating. |
|
Integrate with configuration management systems to ensure consistency and traceability of RxSWIN. |
|
We have established a system that allows us to submit the RxSWIN history required for type certification. |
Implementation examples and industry trends
European trends
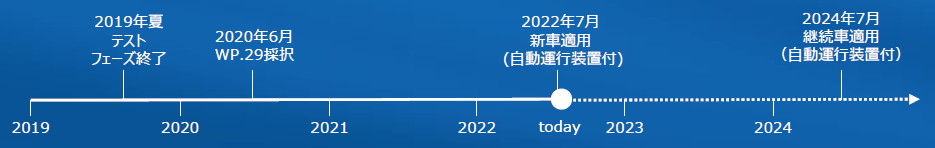
European automakers are now required to implement a Cyber Security Management System (CSMS) and a Software Update Management System (SUMS). These systems will be required for new vehicles that will obtain type approval after July 2022, and major automakers are already working to establish these systems.
Domestic trends
The Ministry of Land, Infrastructure, Transport and Tourism is currently developing a system in accordance with UNECE regulations, and is moving towards making the introduction of CSMS/SUMS a requirement for obtaining type approval. From 2022 onwards, the introduction of CSMS/SUMS will be required for new vehicles, and domestic automakers and suppliers are rushing to comply. With the increasing importance of software safety and update management, particularly with the spread of over-the-air updates and connected cars, the development of SUMS is becoming an urgent issue.
Related solutions and inquiries
From the above, we understand that cybersecurity measures are necessary for vehicles as well, but there may be cases where you don't know what to do or where to start.
In such cases, ETAS provides services such as cybersecurity consulting and training to help customers solve their problems.
In addition, Macnica can make proposals from both software and hardware perspectives regarding the security that is actually installed in vehicles.
Please check the related URL below to see what kind of proposals we can offer.
Solutions from ETAS and Infineon that can be offered by Macnica
Image of the total hardware and software solutions that Macnica can offer
If you have any other concerns or questions about security, or would like to see specific solutions, please feel free to contact us.
ETAS manufacturer information TOP
If you want to return to ETAS Manufacturer Information Top, please click below.
