zero trust

Latest Information
We will use Macnica 's unique perspective and knowledge to explain case studies and measures to strengthen cybersecurity, with a focus on zero trust.
Seminar
これから開催 開催終了 【{{ item.seminarClass }}】{{ item.title }} {{ item.title }}
{{ item.seminar_start_date__display_1 }} {{ item.seminar_place__display_1 }}
service
Macnica provides unique services that support zero trust.
- Support for conceptualizing the ideal image considering the customer's existing environment
- Support for introduction order and roadmap creation
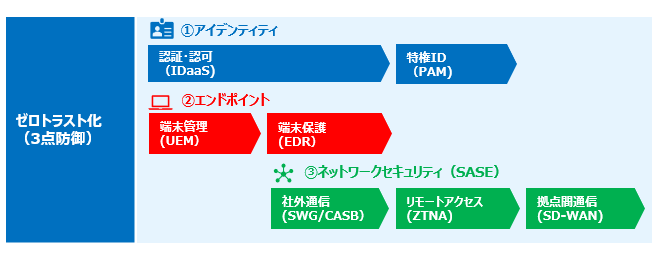
- Organizing the existing increasingly complex ID environment and envisioning the ideal state
- Selection of optimal ID solution and presentation of configuration proposals
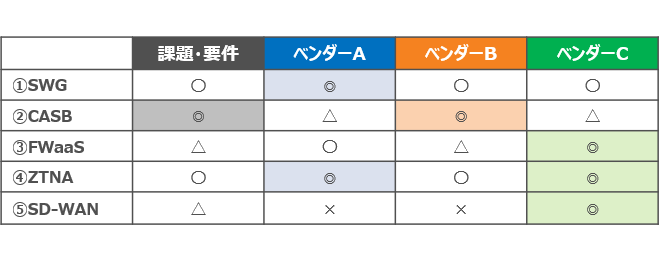
- Organize necessary functional requirements from hearing customer issues
- Presentation of optimal SASE/SSE solutions according to requirements
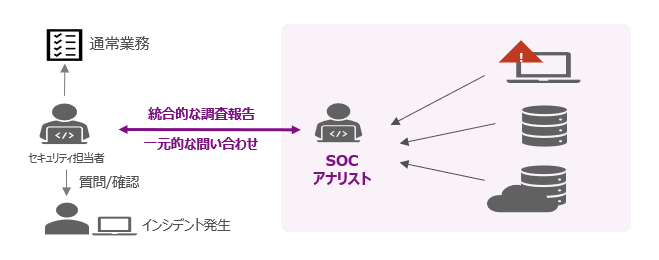
- Significantly shorten incident response time through cross-sectional investigation of multiple logs
- Simplify operations with a single unified SOC contact
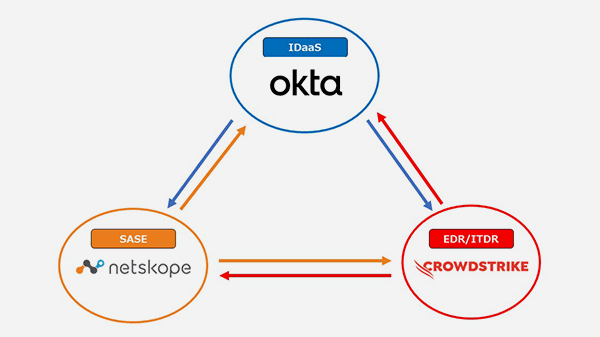
Solution collaboration
We will introduce an image of solution cooperation that combines multiple products on YouTube.
Related product
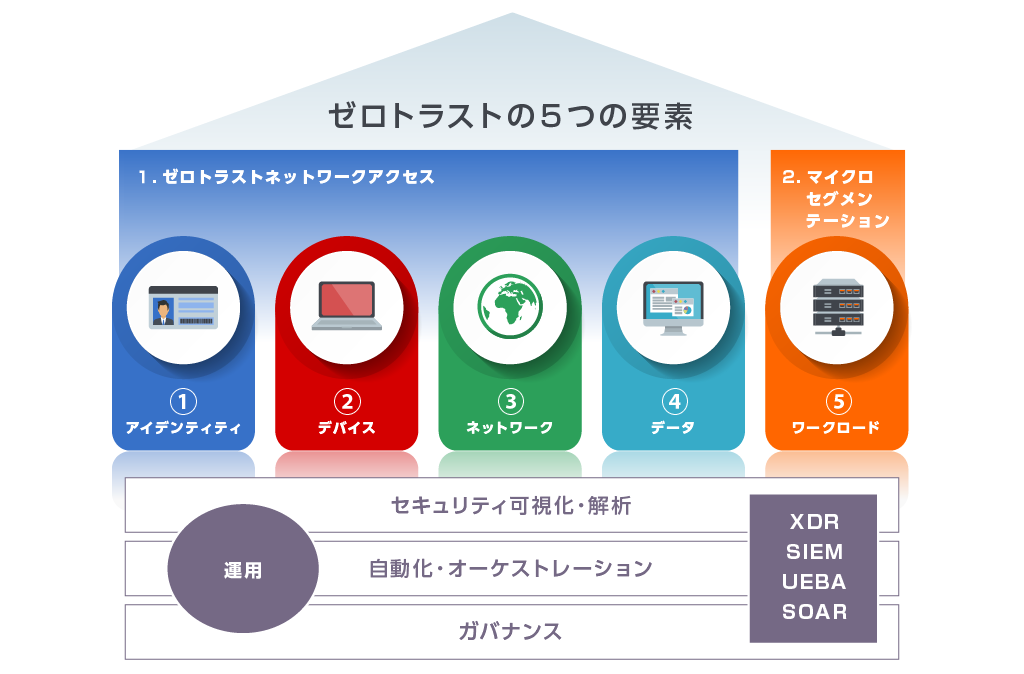
In order to achieve multi-vendor zero trust, we handle a wide range of solutions centered on solutions with a proven track record in each category.
We select products that match the customer's existing environment and provide support from design, construction, and implementation to subsequent operation.
| Two zero trust | 5 elements | product solutions | Solution brief | Macnica Solutions | ||
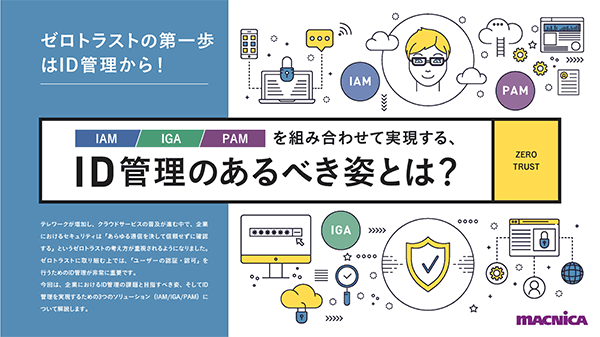
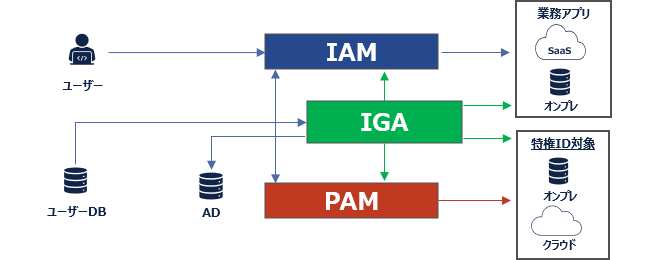
| Achieving secure access “vertical” zero trust | identity |
IDaaS | IAMs | General ID access management | Okta | |
| PAM | Privileged ID access management | CyberArk | ||||
| IGA | ID authority management | Saviynt | ||||
| ITDR | ID threat detection and response | CrowdStrike ITP | ||||
| device |
EDR | Detection and response to device threats | CrowdStrike | |||
| UEM | Integrated management of terminals | Ivanti Tanium |
||||
| Network |
SASE | SD-WAN | Inter-site communication for internal use | Aruba EdgeConnect SD-WAN Netskope |
CatoNetworks | |
| data |
SSE | security service edge | Aruba(Axis) Island Menlo Security Netskope Skyhigh Security |
|||
| Horizontal zero trust measures after internal intrusion | Workload |
microsegmentation | Visualization and control of communication between servers | Illumio Akamai (MSC handling) |
||
| NDRMore | Threat detection and response inside data center | VectraAI | ||||
Inquiry/Document request
In charge of Macnica Zero Trust Co., Ltd.
- TEL:045-476-2010
- E-mail:zerotrust@macnica.co.jp
Weekdays: 9:00-17:00