
About reports
Macnica, primarily through its Security Research Center, has been analyzing targeted attacks (cyber espionage) landing on Japanese organizations since 2014. This report is written to raise awareness, focusing on the analysis results of attack campaigns observed in fiscal year 2024 (April 2024 to March 2025) that attempt to steal confidential information (personal information, policy-related information, manufacturing data, etc.) from Japanese organizations.
Timeline of attacks and industries in which they were observed
In fiscal year 2024, the attack activities of North Korean attack groups have increased compared to attacks up to last year1. In particular, attacks targeting software developers by infecting them with BeaverTail and InvisibleFerret have been actively observed2. In addition, attacks using a backdoor called RokRAT to upload stolen data to legitimate cloud storage have also been observed3. As one of the financial attacks by North Korean attack groups, an attack targeting the SWIFT international remittance system of financial institutions and making large amounts of illegal remittances was reported around 20164. Recently, it appears that attacks targeting cryptocurrency-related developers and accessing wallets of exchanges to which the developers have access to illegally obtain cryptocurrency have become more active5. Next, attack activities using the PlugX malware by the TELEBOYi attack group, which have been observed since last year, and attacks using PlugX that spread via USB by Mustang Panda have also been observed6. In addition, attacks using WinDivert 7 8 to interfere with communication with endpoint security servers to avoid detection have also been observed. In 2025, a zero-day vulnerability attack on Ivanti's VPN device was observed at the same time as last year, and in March, spear phishing aimed at infecting MirrorFace with ANEL 10 11 was actively observed. Although not listed in the table, multiple attacks have been observed in which attacks exploiting vulnerabilities in VPN devices were infiltrated, mainly at overseas manufacturing bases, and were detected in the system and network reconnaissance phase of the LotL attack.

Table 1. Timeline of observed attack group activity (FY2024)
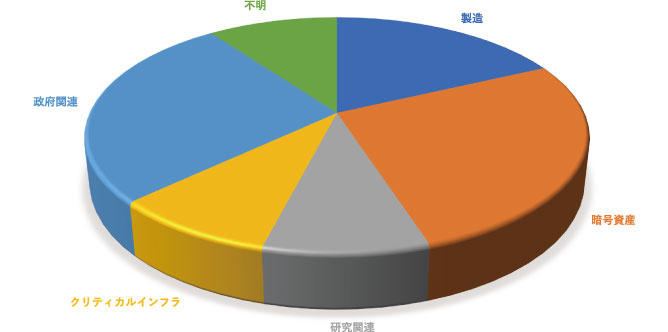
Figure 1. Percentage of target industries (FY2024)
As with the previous fiscal year, spear phishing and intrusions from external public assets were observed as the most common intrusion patterns for targeted attacks. There has been an increase in social engineering that aims to infect computers through messages sent to accounts such as LinkedIn other than email. Also, as with the previous fiscal year, there were cases where targeted malware infections were observed via USB, and there were also cases where the intrusion route was unclear.

Figure 2. Attack surface ratio (2024)
- executive summary
- Timeline of attacks and industries in which they were observed
- Attack summary
- May 2024
- June 2024
- October 2024
- December 2024
- January 2025
- March 2025
- New TTPs, RATs, etc.
- LotL Attack
・Attack Overview
・Observation examples
・Towards detecting LotL attacks
- Analysis of the Attack Campaign Leveraging CVE-2025-0282
・Tools installed by attackers
・Activities after the initial compromise
- Consideration of TTPs and countermeasures for public appliance breaches
- LotL Attack
- Vulnerability Review 2024
- VPN device vulnerability response status
- Vulnerability in Ivanti Connect Secure etc. (CVE-2025-22457)
- FortiGate vulnerability (CVE-2024-55591)
- TTPs (tactics, techniques, procedures) by threat group
- Threat Detection and Mitigation Considered from TTPs
- Malware delivery, attacks, and intrusion
- Installed RAT, remote control (for C2 server)
- indicator of detection
- https://www.macnica.co.jp/business/security/security-reports/pdf/cyberespionage_report_2023.pdf
- https://jp.security.ntt/tech_blog/contagious-interview-ottercookie
- https://asec.ahnlab.com/jp/65053/
- https://piyolog.hatenadiary.jp/entry/20160315/1458056459
- https://www.npa.go.jp/bureau/cyber/koho/caution/caution20241224.html
- https://www.justice.gov/archives/opa/pr/justice-department-and-fbi-conduct-international-operation-delete-malware-used-china-backed
- https://www.lac.co.jp/lacwatch/report/20240605_004019.html
- https://github.com/basil00/WinDivert
- https://cloud.google.com/blog/topics/threat-intelligence/ivanti-connect-secure-vpn-zero-day?hl=en
- https://www.trendmicro.com/ja_jp/research/24/j/new-spearphishing-by-earth-kasha.html
- https://www.welivesecurity.com/en/eset-research/operation-akairyu-mirrorface-invites-europe-expo-2025-revives-anel-backdoor/