Lean Seeks
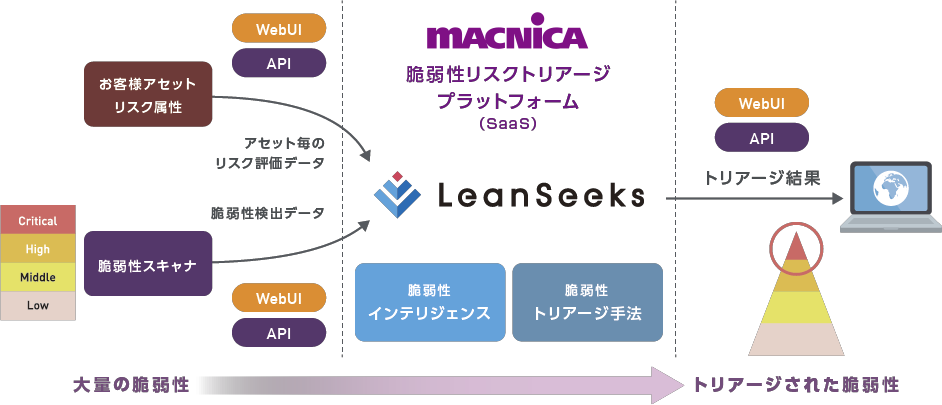
LeanSeeks

Instantly triage high-volume security vulnerabilities
Detected in large numbers and cannot be dealt with in time
Vulnerability determination becomes a bottleneck

is expensive

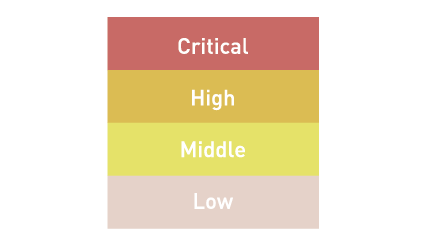
It is important to focus on "truly high-risk" vulnerabilities
(*About 4% of all vulnerabilities are actually exploited.)
*Quoted from CISA Binding Operational Directive 22-01, US Department of Homeland Security

Automatically determines the need for action and assigns priorities (= triage).
Vulnerability response can be greatly improved in efficiency and accuracy.
Features
Triage that reflects the actual risk
A proper risk assessment of a vulnerability requires consideration of the nature of the vulnerability and the nature of the asset, and the CVSS Basic Score has limitations. The existence of attack code that affects risk assessment and the comprehensive triage judgment that evaluates various risk attributes of customer assets in parallel can be automated, greatly reducing vulnerability assessment costs and increasing accuracy.

Utilize the vulnerability scanner that the customer is using as it is *1
Currently, various security products and public cloud services are equipped with functions to scan software vulnerabilities. Deploying a high-accuracy, dedicated vulnerability response product is often expensive, so you can leverage the vulnerability scanner functionality your customers already use.
*1 As of February 2022, the supported vulnerability scanner function is Palo Alto's Prisma Cloud. We plan to gradually expand the supported vulnerability scanners.

Compatible with cloud-native environments
While the adoption of cloud-native technologies, such as containers, is accelerating, most of the time vulnerability responses rely on human judgment. LeanSeeks accelerates vulnerability response and development speed through a triage approach that assumes the existence of a container environment, enabling the promotion of essential DevSecOps.
Operation can be automated using API
In addition to the WebUI, it is possible to automate the detection of vulnerabilities that require daily triage and countermeasures by utilizing the API (*some functions are limited).

Click here for information on features and pricing
How to use
LeanSeeks is provided as SaaS, so there is no need to build a separate server for scanning. In addition, since the output of your vulnerability scanner (* limited to tools supported by LeanSeeks) is used, there is no need to install agents on each instance. You can use the following steps to triage vulnerabilities.
Vulnerability triage steps
- Upload detection data (JSON files, etc.) from corresponding vulnerability scanners to LeanSeeks
- Set risk attributes for each asset (instance) that makes up an application on LeanSeeks
- Perform triage and check results on LeanSeeks
Use Case

Development team
- Accurately grasp the risk situation in the development phase
- Focus and respond to high risk priority vulnerabilities
- Avoiding rework from the post-process
Even development teams without security expertise can make correct risk judgments

security team
- Accurately understand the vulnerability risks contained in each application
- In the event of a high-risk vulnerability, work with the development team to respond
- Use the triage results as criteria for dealing with the development team
Accurate risk control without overburdening the development team
Usage flow



Frequently Asked Questions
| Which vulnerability scanners do you support? | All vulnerability scanners that can output CVE are supported. |
| サービスは日本国内から提供されますか? | Yes, it will be provided from the data center in Japan. We do not store data overseas. |
| What do I need to prepare to use it? | Vulnerability data detected by a vulnerability scanner is required. In addition, it is necessary to define risk attribute information in advance, but please contact us for details. |
| Are there any features to prevent unauthorized use by others? | You can use security functions such as two-factor authentication and connection source IP restriction. |
Download materials
Thank you for your interest in this service.
We will send you the details of the materials by e-mail, so please request from the following.
Inquiry/Document request
Macnica LeanSeeks
- TEL:045-476-2010
- E-mail:leanseeks-sales@macnica.co.jp
Weekdays: 9:00-17:00