CTEM(Continuous Threat Exposure Management)
What is CTEM?
CTEM (Continuous Threat Exposure Management) is a security measure that continuously discovers, evaluates, verifies, and improves all attack surfaces and risks (exposures) that exist within an organization. It significantly expands on traditional vulnerability management and achieves comprehensive risk management, including setting defects and misconfigurations for which no CVE exists.
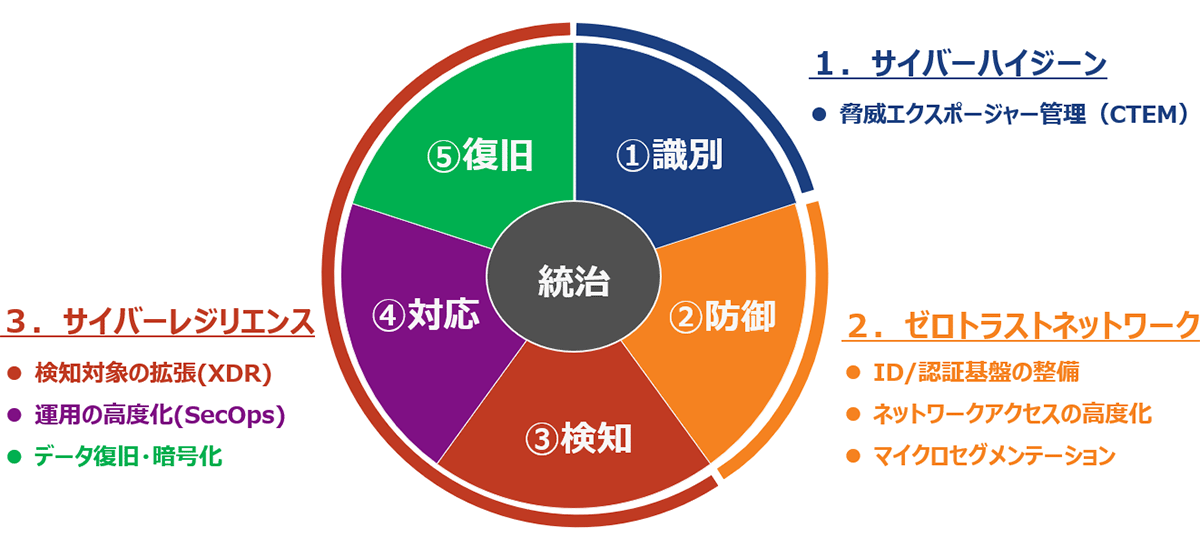
CTEM is a core technology of "cyber hygiene" and plays a role in the "identification" stage of the NIST Cybersecurity Framework. It works in conjunction with Zero Trust Network (defense) and Cyber Resilience (detection, response, and recovery) to build a comprehensive security posture.
Three Frameworks
Background of the growing interest in CTEM
In terms of cyber threat trends as of 2025, ransomware attacks will remain the biggest threat for the fifth consecutive year, with supply chain attacks and attacks that exploit system vulnerabilities also ranking highly.
Attackers are now targeting not only known vulnerabilities but also "risks that increase the probability of an attack being successful even without a CVE," such as misconfigurations and excessive privileges, and there is an increasing need to manage all of these as risks (exposures).
Deciphering the IPA Top 10 Security Threats of 2025
- Ransomware attacks remain the number one threat for the fifth consecutive year
- Attacks targeting vulnerabilities, outsourcing partners, and VPN devices, which are breeding grounds for ransomware attacks, also ranked high, taking second, third, fifth, and sixth places.
- The rise of a new cyberattack: business email compromise
- Internal threats such as internal fraud and information leaks continue to rank highly
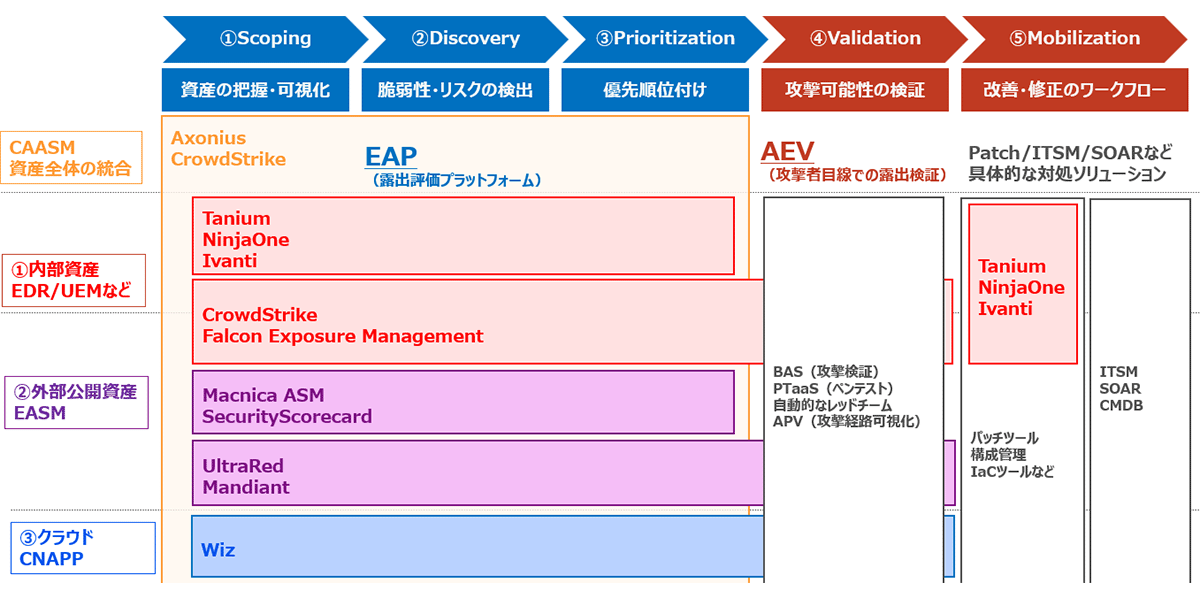
Five processes of CTEM
CTEM is implemented in a five-step cycle:
- Scoping
Clearly define the scope of IT assets to be managed. It is important to set a comprehensive range of assets, including on-premise, cloud, SaaS, and IoT devices. - Discovery
Automatically visualize and discover assets and exposures, including unmanaged assets, misconfigurations, excessive privileges, and unpatched systems. - Prioritization
Prioritize threat exposures by comprehensively assessing CVSS scores, exploitability, business impact, and asset criticality to determine the order in which they should be addressed. - Validation
We verify the possibility of actual attacks from an attacker's perspective, utilizing penetration testing and BAS (Breach and Attack Simulation) techniques to confirm whether theoretical risks pose actual threats.
Continuous Threat Exposure Management (CTEM)
- Identify and prioritize all exposures, including vulnerabilities and configuration errors (diagnosis phase)
- Verify whether the threat actually reaches the target, and if there is a problem, improve the system by applying patches, etc. (Execution phase)
- Scoping
Set the scope of management - Discovery
Visibility and discovery of assets and exposures - Prioritization
Prioritizing threat exposures - Validation
Verification of attack feasibility from an attacker's perspective - Mobilization
Addressing dangerous vulnerabilities and exposures
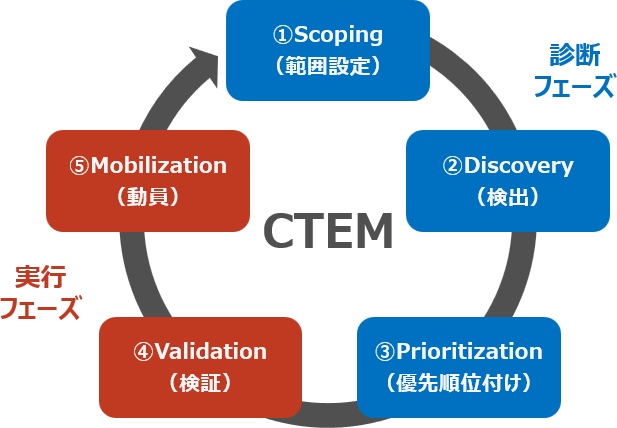
Rapidly address dangerous vulnerabilities and exposures by applying patches, changing settings, and reviewing access controls, all in conjunction with automated tools and workflows.
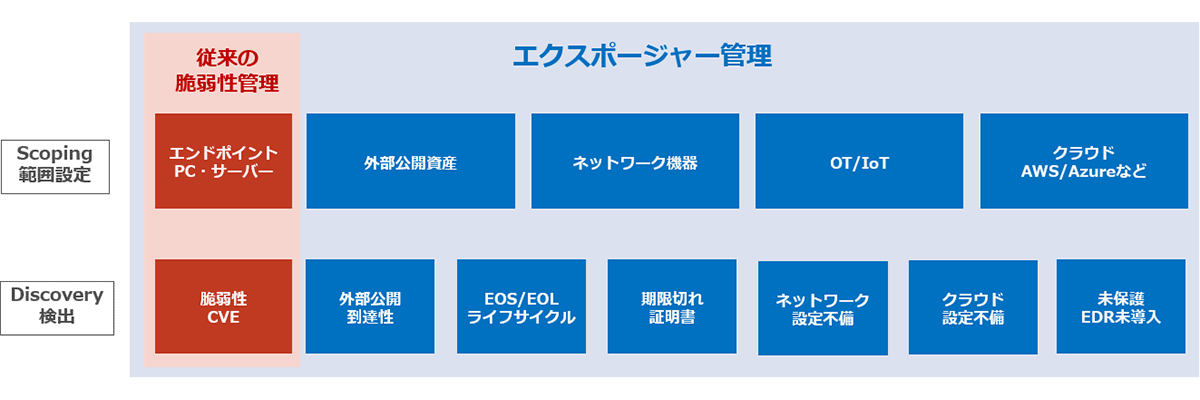
Differences from traditional vulnerability management
In contrast to traditional CVE-centric vulnerability management, CTEM manages all factors that increase the probability of an attack being successful, such as external disclosure, misconfigurations, lifecycle, and expired certificates, as exposure.
Since only a few percent of exposures are actually exploited in attacks, it is important to focus on exposures that have the potential to cause serious incidents.
From vulnerability management to exposure management
- Exposure = conditions that increase the probability/impact of intrusion, lateral movement, and information leakage
- Any risk that increases the probability of an attack succeeding, even without a CVE, is an exposure
- Example: "Externally available network equipment that has reached EOL"
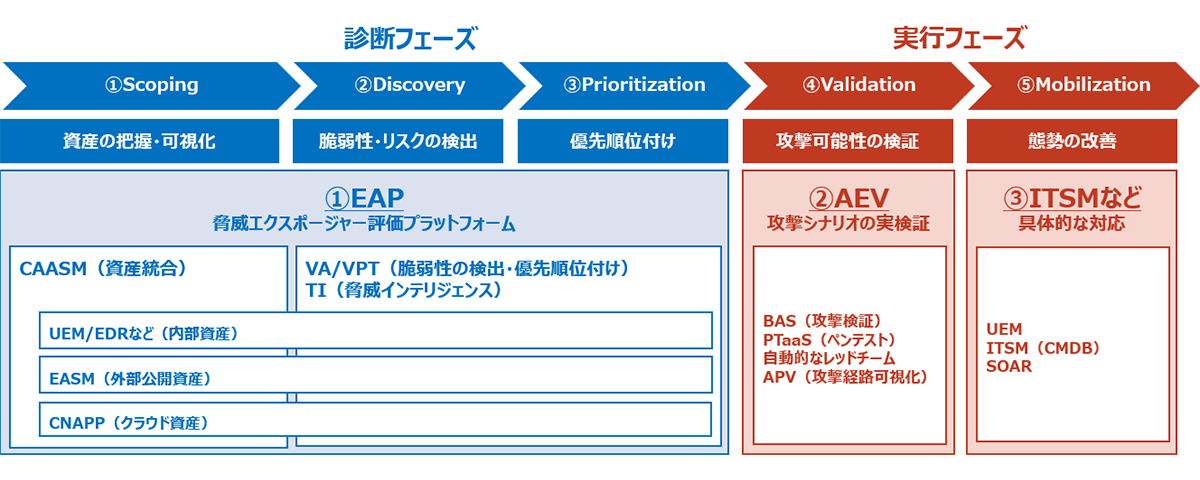
Technological elements that make up CTEM
CTEM is not a single solution, but rather an integration of multiple technologies.
- Diagnostic Phase
- CAASM (Cyber Asset Attack Surface Management): Integrated asset management
- EASM (External Attack Surface Management): External public asset management
- CNAPP (Cloud Native Application Protection Platform): Cloud Asset Management
- VA/VPT (Vulnerability Assessment/Penetration Testing): Vulnerability assessment and penetration testing
- Execution Phase
- EAP (Exposure Assessment Platform): Exposure assessment platform
- AEV (Attack Exposure Validation): Attack probability verification
- BAS (Breach and Attack Simulation): Breach and attack simulation
- APV (Attack Path Visualization): Visualizing attack paths
Solutions that enable CTEM
- CTEM is a concept and cannot be realized with a single solution.
- Solutions that aggregate and integrate multiple functions such as EAP and AEV are also emerging.
Effects and benefits of implementation
- Increased risk visibility: Discover previously overlooked attack surfaces
- Improved response efficiency: Efficient resource allocation based on priority
- Optimizing security investments: Allocating budgets based on actual risks
- Incident Prevention: Proactive security to prevent attacks before they happen
- Strengthening Compliance: Building a Continuous Vulnerability Management System
Macnica 's CTEM-related solutions
Macnica offers the following CTEM-related solutions.
Please feel free to contact us for more details.
Typical solutions for realizing CTEM
Related Videos
For more details, click on the thumbnail and watch now (register for free membership)

