In 2024, amidst the unstable global situation, cyber attacks targeting OT (operational technology) and ICS (industrial control systems) reached record levels in terms of both method and scale. This report summarizes the year's threat trends, case studies, risks to consider, and recommendedcountermeasures.
Introduction
This report systematically explains cybersecurity trends in the OT/ICS field based on the latest case studies and data collected and analyzed by Dragos, and clarifies specific defensive measures that on-site managers and security personnel should take.
[Video message from Dragos CEO Robert M. Lee on the occasion of the report release]
Founder and CEO of Dragos, Inc.
Evolution of the global threat environment and attack methods
The 2024 threat landscape for OT/ICS was heavily influenced by geopolitical tensions around the world, including Ukraine, Russia, the Middle East, and Asia. Particularly notable was the active infiltration of the industrial sector by a wider range of attackers, including not only state-sponsored APT groups, but also hacktivists and ransomware gangs.
Key numerical highlights (excerpt from PDF graph)
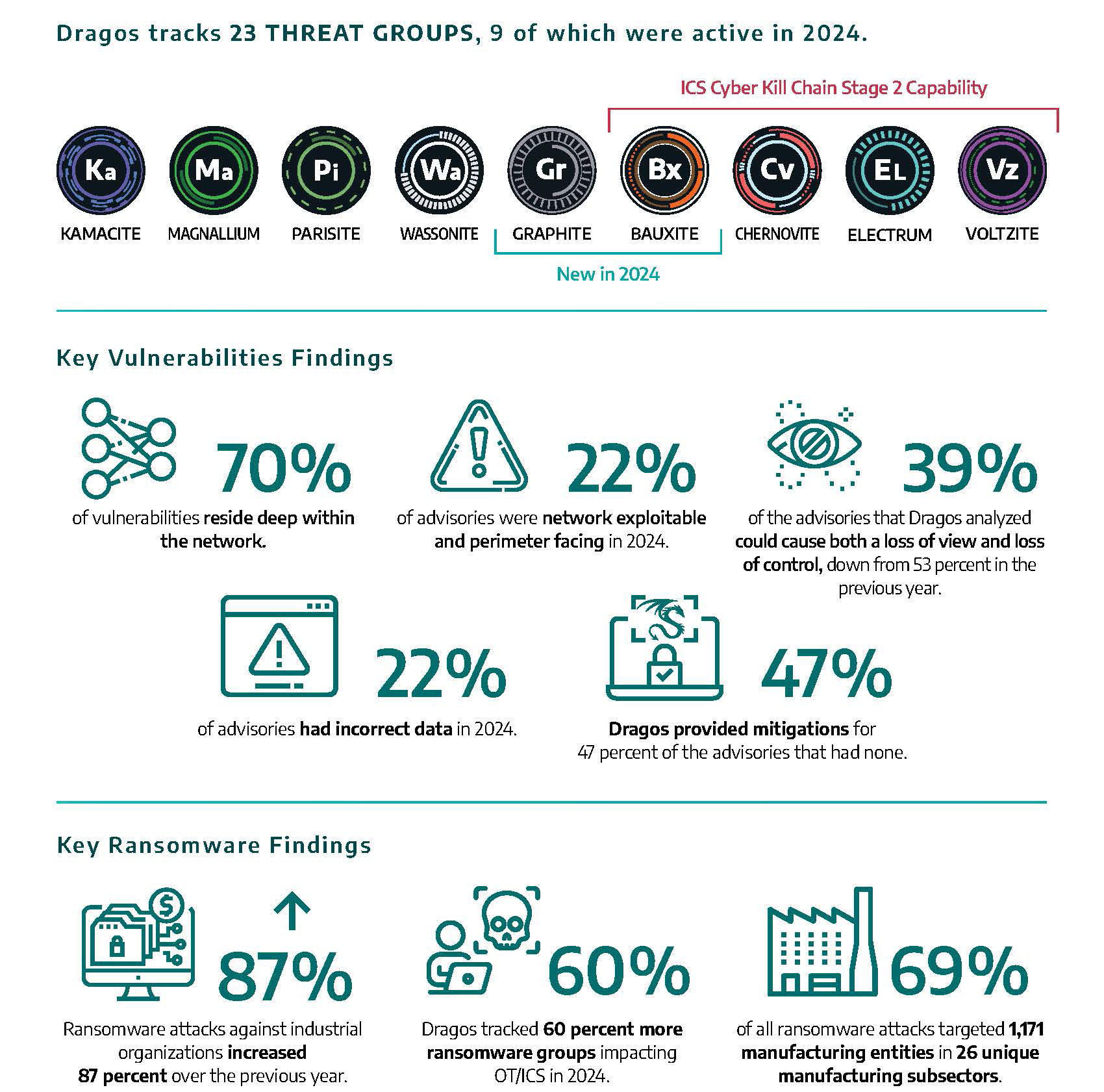
- 2024 Year OT/ICS ransomware attacks on 87% Increase, Dragos The number of ransomware groups tracked by 60% increase.
- 69% of ransomware attacks target the manufacturing industry.
- twenty three Threat Group of Dragos is tracking, and then 9 t but 2024 Active in .
- 22% of vulnerability advisories contain errors, and 70% of vulnerabilities reside deep within the network.
The characteristics of the attack are:
- Targeting security gaps such as default settings, public devices, and legacy devices
- After intrusion, it spreads within the system, and then moves laterally and deploys ransomware.
- There are many cases where important processes cannot be stopped safely, causing business operations to stop and making recovery difficult.
Major threat groups and attack examples
- KAMACITE / ELECTRUM: Attacked Ukrainian power generation facilities and telecommunications companies in line with Russian military objectives. Launched new malware (Kapeka, etc.) and a Linux wiper (AcidPour).
- VOLTZITE (Volt Typhoon series): Believed to be a Chinese state-sponsored attacker, it stole network maps (such as GIS) from SOHO routers and critical infrastructure around the world. It is characterized by living-off-the-land attacks that exploit vulnerabilities in existing equipment.
- New groups (GRAPHITE, BAUXITE): Against the backdrop of the situation in Ukraine and the Middle East, they are expanding their phishing, malware injection, SSH device abuse, and remote control attacks.
Malware, ransomware, and increasing "disruption of business" attacks
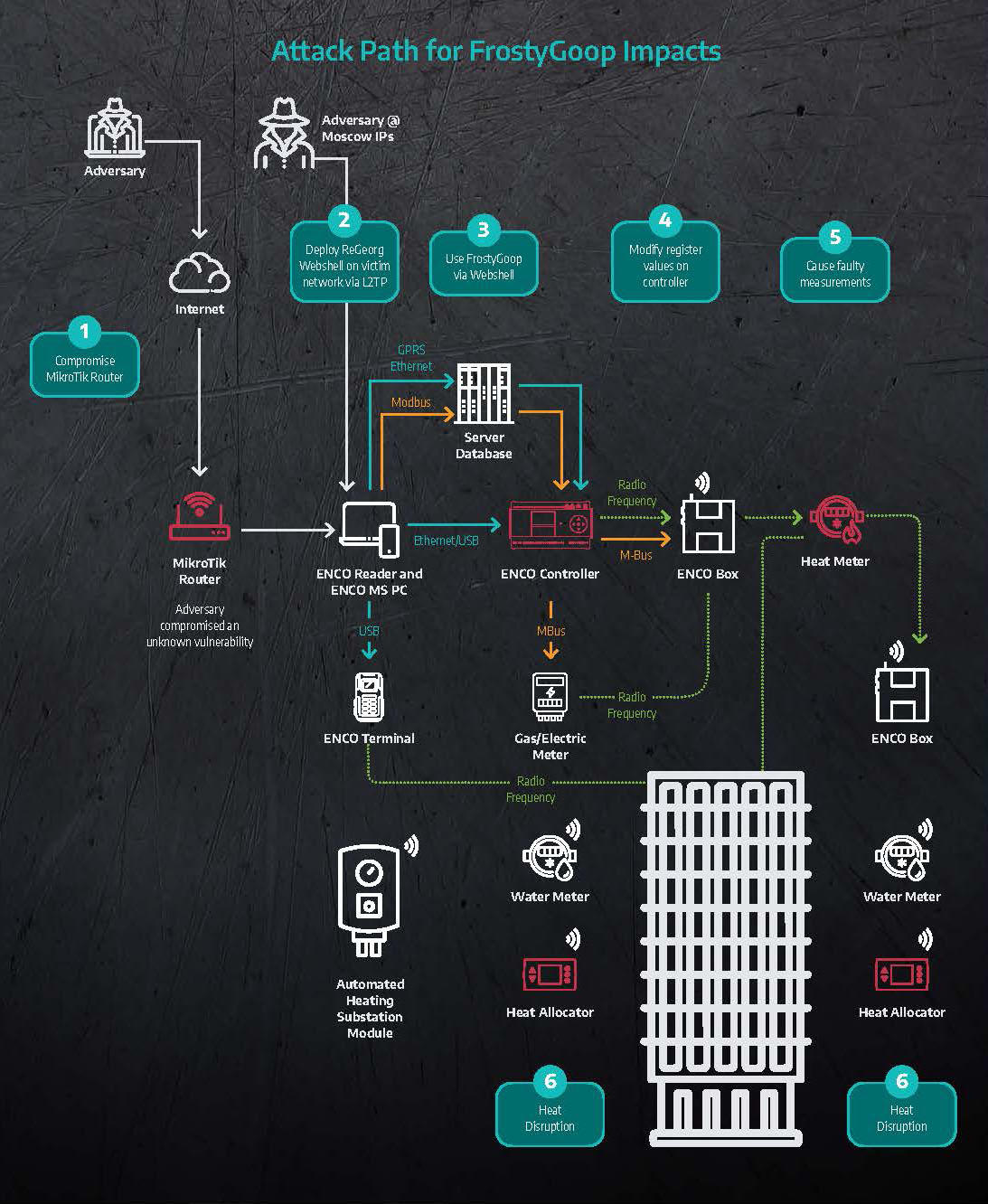
In 2024, a series of malware specific to ICS devices emerged (e.g., Fuxnet, FrostyGoop, etc.).
- Fuxnet: Launched an attack against Russia's Moskollektor, physically destroying and rendering inoperable its sensor network and gateway devices.
- FrostyGoop: Malware used to attack Modbus devices that caused heating outages in over 600 buildings in Ukraine.
Ransomware has also evolved, with attacks on the manufacturing industry becoming prominent in 2024. There have been many cases where ransomware has moved laterally from IT networks to the OT domain, causing factory shutdowns and supply chain disruptions. (LockBit, RansomHub, etc. have led large-scale attacks.)
Vulnerabilities, supply chains, and IoT risks
- Unupdatable or "insecure-by-design" vulnerabilities pose unique risks in industrial equipment.
- Third-party components and IoT devices (e.g., Mirai botnet infection cases) are becoming more targets of attack.
- Windows-specific risks such as DLL hijacking are also common, and have been widely used in APT attacks, starting with Stuxnet in the past.
Recommended defense points (SANS ICS 5 Critical Controls)
It has been pointed out that we need to move away from passive defensive and "reactive security," and the following five items have been repeatedly recommended.
- Incident response plan development and training
- Building a "defensible architecture" by dividing the network and reviewing the scope of disclosure
- Introduction of monitoring and visualization solutions specialized for OT
- Safety design for vendor and remote connections
- Risk-based vulnerability management and asset identification

lastly
Geopolitical influences will continue to pose high security risks to OT in 2025. Ransomware and state-sponsored attacks are on the rise, and technologies and threats continue to change. To protect industries in this environment, it is essential to update defense measures based on the latest threat information. We hope this report will help readers put defense measures into practice and strengthen their organizations' security.
