Introduction
The Anti-Phishing Working Group has updated its Anti-Phishing Guidelines and released the 2024 edition [1]. Phishing reports to the Working Group increased from 10,000 in January 2021 to 90,000 in April 2023, and the Financial Services Agency issued a warning against fraudulent internet banking transfers, making phishing a social problem. The Working Group updates its guidelines every year to keep up with the latest developments.
The target audience of the guidelines is "users and website operators who may be victims of phishing," and the countermeasures prescribed in the guidelines cover a wide range of topics, including web operation, email phishing, and SMS smishing.
While the guidelines contain comprehensive countermeasures, we have also received concerns about how to use them to address individual issues. With regard to Smishing via SMS, we are often asked where to start in dealing with not only damage caused to our own organization's website, but also smishing attacks impersonating our own organization.
In this column, we will explain the updates to the anti-phishing guidelines and how to use the guidelines to respond to smishing attempts that impersonate your organization.
Summary of the 2024 Anti-Phishing Guidelines
The structure of the guidelines and an overview of each chapter are summarized in Table 1. Website operators are expected to use the guidelines in the following steps to protect website users from phishing scams.
(2 Chapter) Confirmation of implementation of five important items
(Chapter 3) Requirements twenty two Check the implementation of the items
(Chapter 4) Confirmation of implementation of measures
In this way, you can review the contents of each chapter in order and understand what your organization needs to do. If there are any areas where measures have not been taken or are insufficient, you can make improvements to those areas.
|
chapter
|
title |
Overview |
|
1.
|
Introduction |
|
|
2.
|
Five important points in the guidelines for preventing phishing |
|
|
3.
|
Web In the operator |
|
|
4.
|
Anti-phishing |
|
|
5.
|
For users |
|
|
6.
|
appendix |
|
Table 1. Composition and overview of the Anti-Phishing Guidelines (2024 edition)
Five points have been listed as updates from the previous year's edition, with ease of use being given great importance.
- Reviewed the flow of content. Explanations of basic concepts and glossary moved to appendices.
- Deleted items due to changing circumstances to make the document more concise.
- Separating requirements from how to implement them
- Added anti-phishing checklist to appendix
- Other updates to the latest information
These updates make the guidelines even easier to use.
How to use the guidelines to combat smishing
SMS is a basic function that all mobile phones have, and its use is expanding due to its convenience, such as the ability to send and receive messages using a phone number, and the fact that messages pop up on smartphone screens and are said to have a high open rate. As the use of SMS expands due to its convenience, smishing via SMS has become a social issue, and this issue has been taken up as one of the main themes by the Ministry of Internal Affairs and Communications' working group on measures against inappropriate use [2].
The challenge with smishing is that even if an organization does not use SMS as a means of communication or only uses it to a limited extent, smishing messages impersonating the organization can occur. As a result, personal information of customers related to the organization is fraudulently obtained, causing problems for the organization's brand.
In order to address these issues, we will consider how to utilize these guidelines from the perspective of dealing with smishing scams that impersonate one's own organization. As mentioned in the previous section, these guidelines are targeted at website operators, so in order to use them with a focus on smishing, it is necessary to select those requirements in the guidelines that are related to smishing and classify them in a way that makes them easy to use.
For classification, we use two axes: a time axis of "prevention, detection, and response" and an axis of the implementing body of "responding within our own organization, requesting other organizations, and educating users."
[Step 1] Select smishing-related requirements from 22 requirements
Decide whether each requirement applies to Email, SMS, or Web, and select the requirement for SMS. Some requirements apply to multiple targets. Make your selection by referring to not only the requirement text, but also the guideline explanations.
As a result, 10 out of 22 are SMS related.
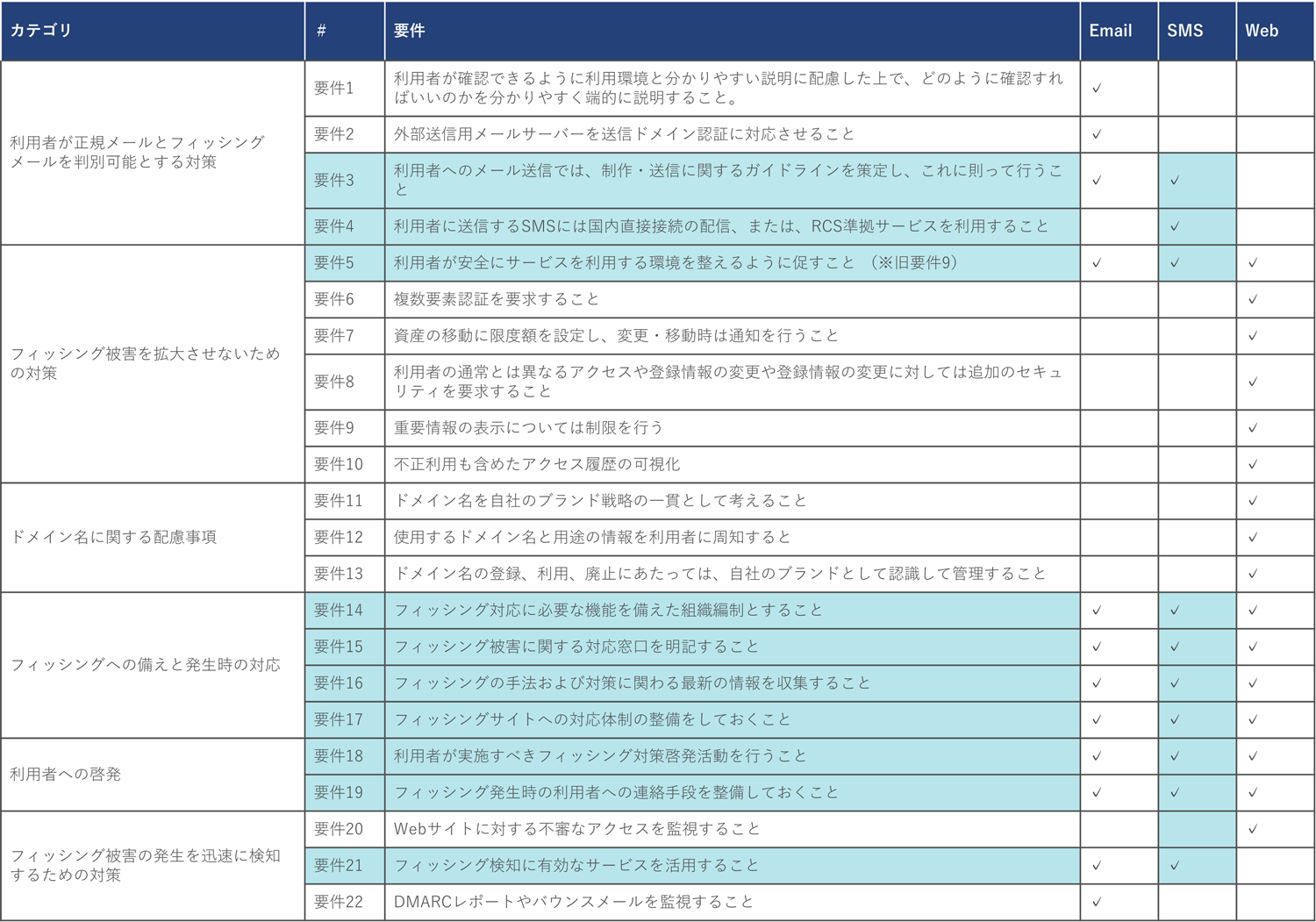
Table 2 Requirements for Email/SMS/Web
[Step 2] Match related requirements between "prevention, detection, and response" and "inside, outside, and users"
The 10 requirements for smishing countermeasures are classified from two perspectives: which phase of prevention, detection, or response each requirement applies to, and whether the response stipulated by the requirement can be completed by one's own organization, whether cooperation with other organizations is required, or whether an appeal to users is required.
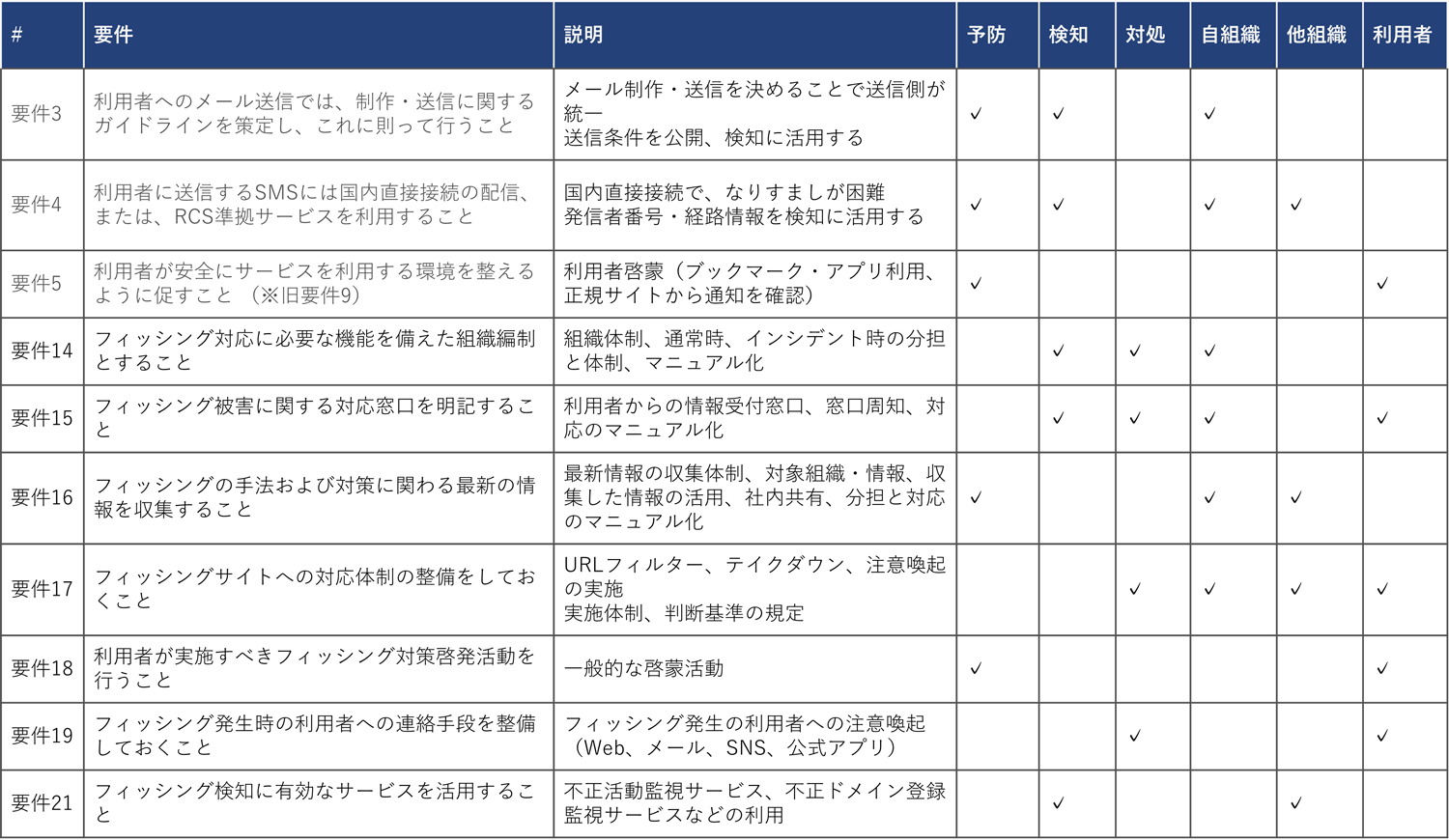
Table 3. Requirements classification
Table 4 shows Table 3 rearranged by "Prevention, Detection, and Response" on the vertical axis and "Our organization, other organizations, and users" on the horizontal axis. The numbers in parentheses indicate the requirement numbers.
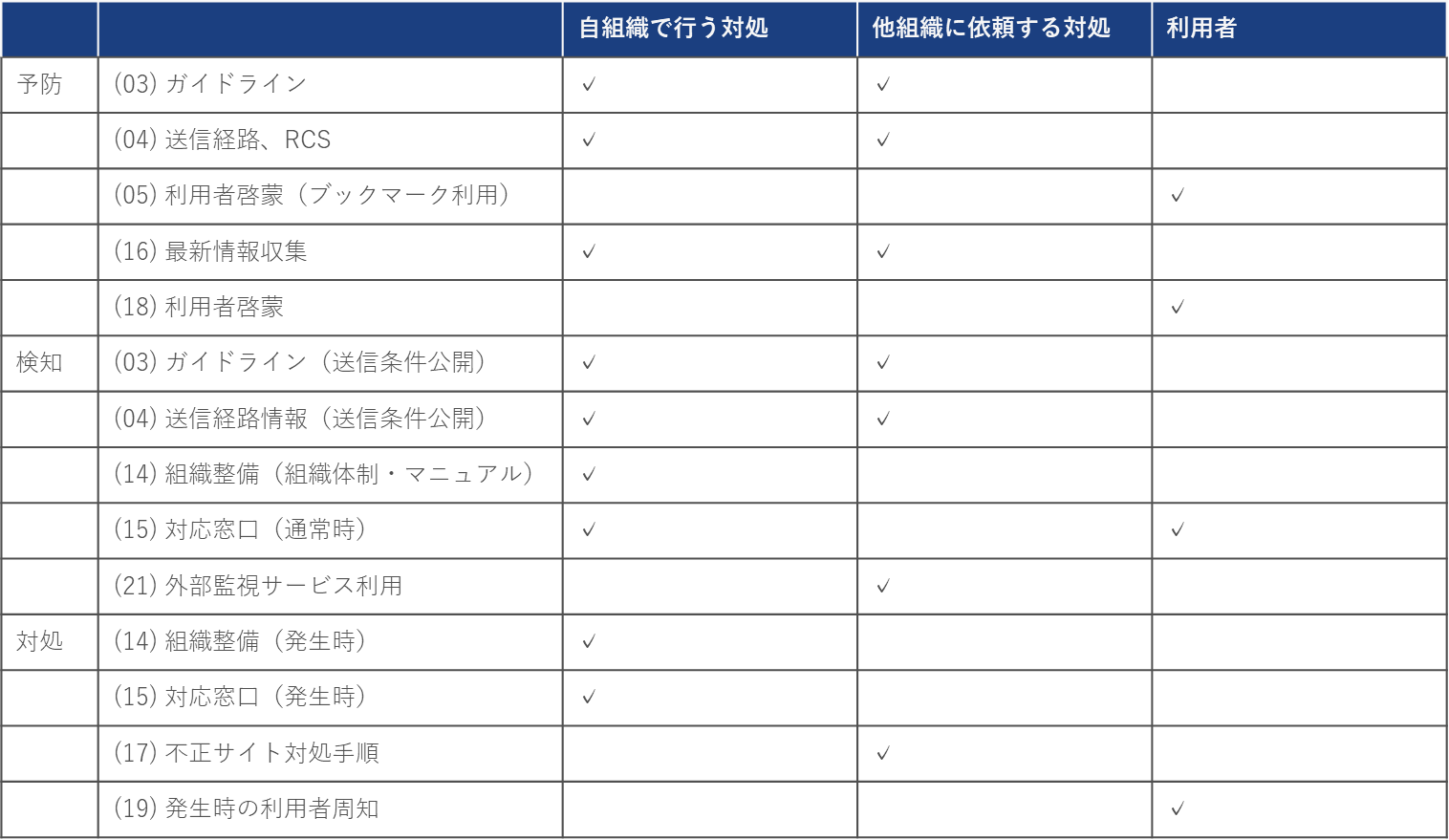
Table 4. Requirements Classification (2)
The following are some possible ways to use this table to take measures against smishing attempts impersonating your organization.
-
Evaluating your organization's response to smishing
We check whether the measures meet the requirements at each step of prevention, detection, and response. When evaluating the requirements, we formulate conditions when applying the requirements to smishing countermeasures, since the requirements described in the guidelines are not necessarily specific to smishing. - Developing a smishing response plan
If your organization is lacking in response to any of the requirements, evaluate the risks of not taking measures and consider the necessity and content of measures. Measures can be completed within your organization or measures for other organizations to take. An example of the latter is publishing the conditions for legitimate SMS sent by your organization so that telecommunications carriers can refer to them to distinguish between legitimate and fraudulent SMS when blocking them. - Measuring the effectiveness of measures
The table can also be used to measure the effectiveness of measures implemented by your organization. Since we assumed the risk reduction when measures are implemented in step 2, we evaluate whether the risk has been reduced as expected after the measures are implemented.
The requirements are written in a generic manner, so when implementing smishing countermeasures based on the requirements, you can make them more specific and detailed so that they can be broken down into things that your organization needs to do.
at the end
Taking advantage of the update of the 2024 edition of the Anti-Phishing Guidelines, we provided an overview of the guidelines and some ideas on how to use them with a focus on smishing. The guidelines were created based on the experiences of our members, and we hope to use them in a variety of ways to help reduce the damage caused by phishing and smishing.
reference
[1] https://www.antiphishing.jp/report/guideline/antiphishing_guideline2024.html
[2] https://www.soumu.go.jp/main_content/000930521.pdf
