product
- Web application vulnerability diagnosis
- Integrated SOC service
- security advisory
- security assessment
- Website security monitoring service
- CrowdStrike Monitoring Operation Support Service
- Active Directory Diagnostic/Monitoring Service
- CSIRT enhancement exercise
- Suspicious email training service
- platform diagnostics
- CSIRT construction support
service

Macnica
Macnica
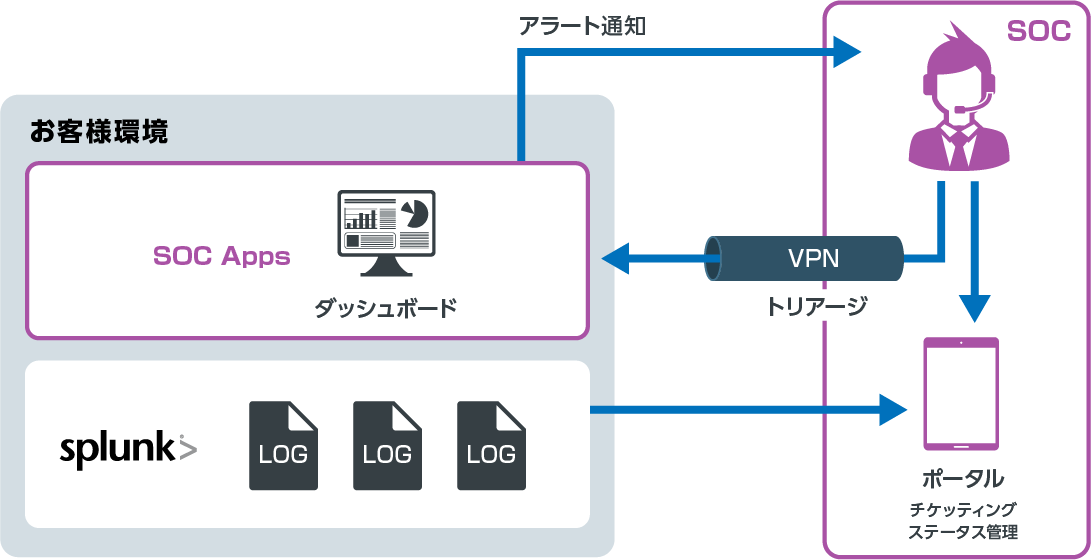
SIEM operation monitoring service
-Support for Splunk security operation-
Correlation analysis and triage using Splunk Reducing the customer's operational burden
Insufficient security knowledge, scrutinizing a large number of alerts, considering countermeasures...
We will solve your operational problems.
- 24/365 security monitoring using your Splunk
- Investigate raw logs and propose countermeasures to customers
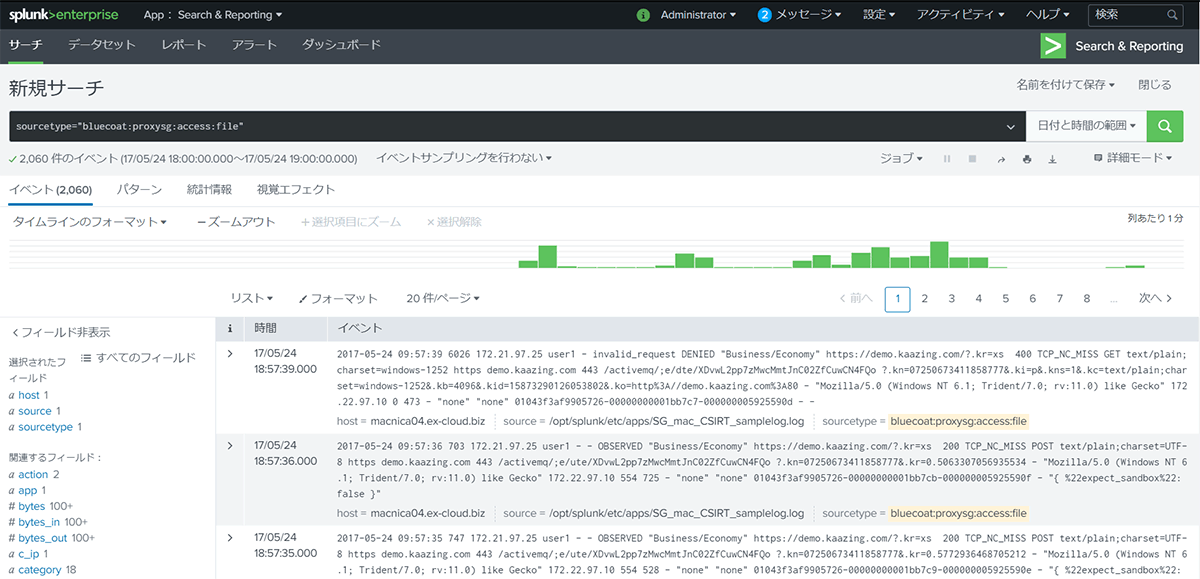
- Customers can freely use logs stored in Splunk
*Splunk, server, VPN are not included in the content of this service. Please contact us separately.
Extensive alert research and response advice from analysts
Customers can continue to use Splunk as a data analysis platform
It is not just a notification of an alert, but also provides advice on how to deal with it.
- Analysis of detected communication for threats
- Analyze the scope of threat impact
- Consideration of countermeasures against threats
- Escalation of analysis results
Fee structure
- The price is determined by the type of monitoring target and the number of employees.
- It will be an annual contract.
*Please contact us for details
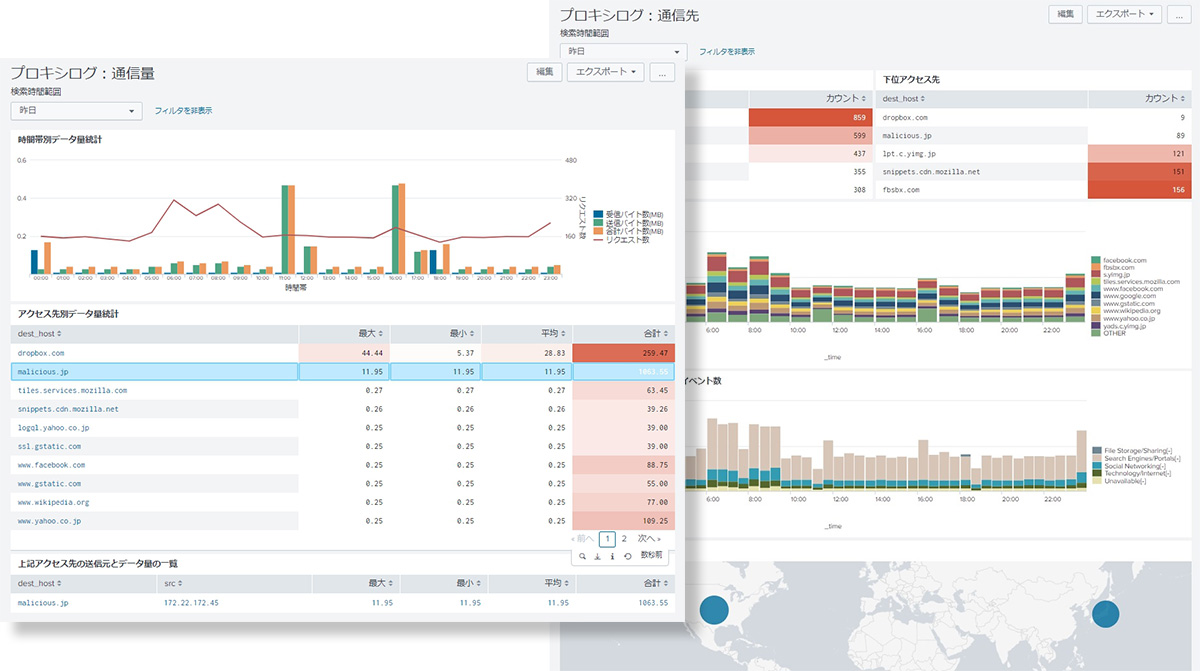
SOC App image
View alerts and event statistics in your Splunk dashboard.
Customers can freely view raw logs from there.
Media introduction
SIEM operation monitoring service was introduced in the media.
Inquiry/Document request
In charge of Macnica Security Service Co., Ltd.
- TEL:045-476-2010
- E-mail:sec-service@macnica.co.jp
Mon-Fri 8:45-17:30