product
- Web application vulnerability diagnosis
- Integrated SOC service
- security advisory
- security assessment
- Website security monitoring service
- CrowdStrike Monitoring Operation Support Service
- Active Directory Diagnostic/Monitoring Service
- CSIRT enhancement exercise
- Suspicious email training service
- platform diagnostics
- CSIRT construction support
service

Macnica
Macnica
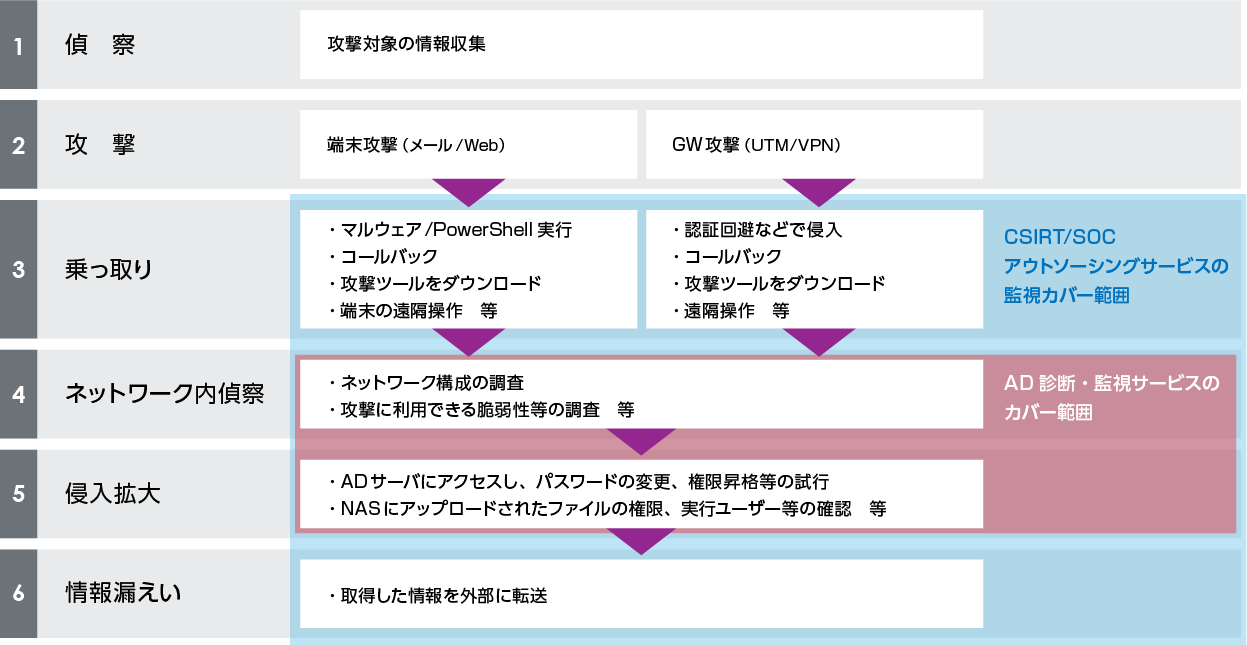
Evolutionary targeted attacks, which can be called exposure-type ransomware/destruction-type ransomware via e-mail, such as device vulnerabilities and EMOTET, are being carried out frequently, and there have been many reports of damage caused by hijacking of Active Directory. If the Active Directory is hijacked, important and confidential information within the company will be stolen and published on the dark web, or the company itself will be forced to stop its activities due to new ransomware, and it will be forced to pay a ransom to respond. fall into. By using this service, it is possible to detect and respond to threats of attacks targeting Active Directory at an early stage.
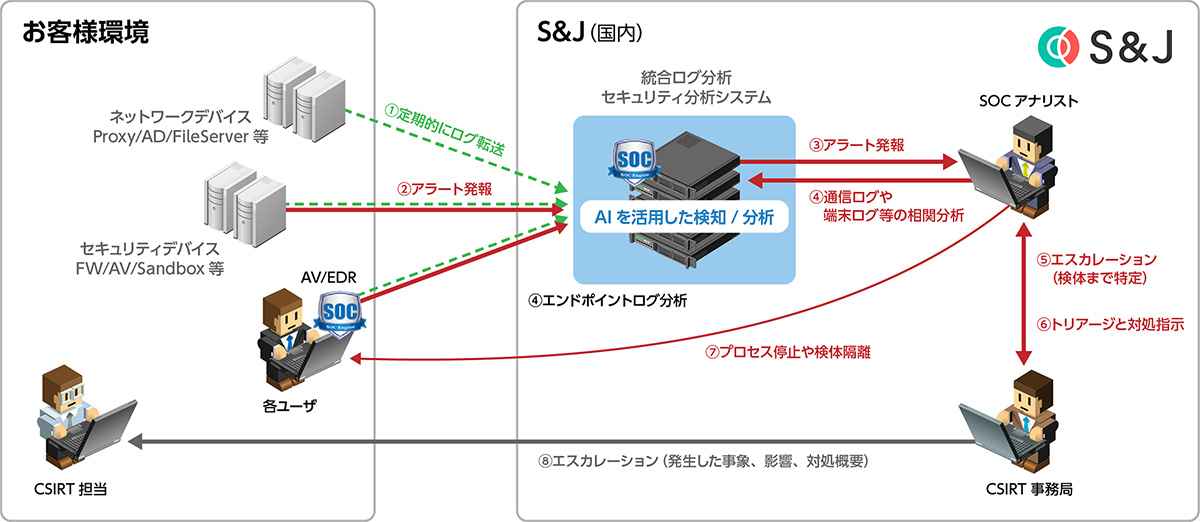
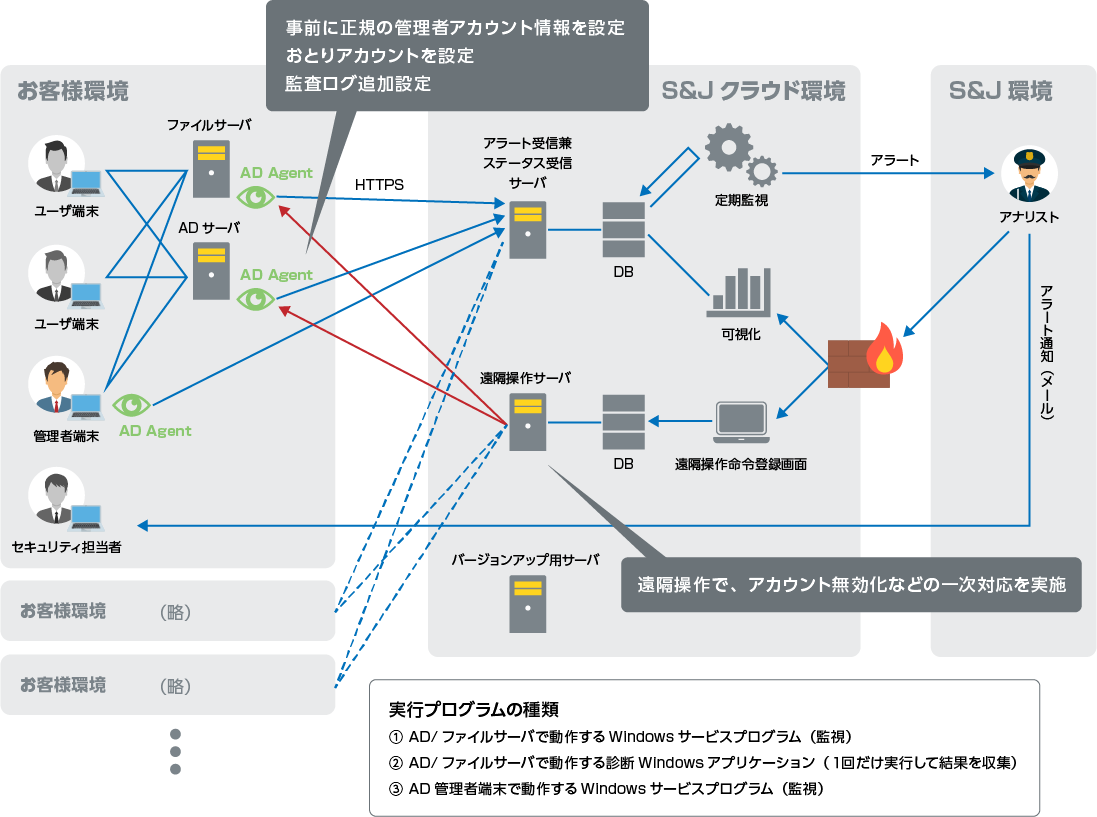
Service outline diagram
Features of this service
- With the diagnostic service, it is possible to set various logs necessary for AD monitoring and detect theft of administrator accounts, suspicious PowerShell execution, group policy tampering, etc.
- Detecting threats that cannot be detected by SIEM or EDR is possible because it is equipped with logic specialized for attack detection against AD and administrator terminals by analyzing AD agents and analysts installed in AD.
- 24/7 monitoring for early attack detection, escalation, and remote remediation if needed
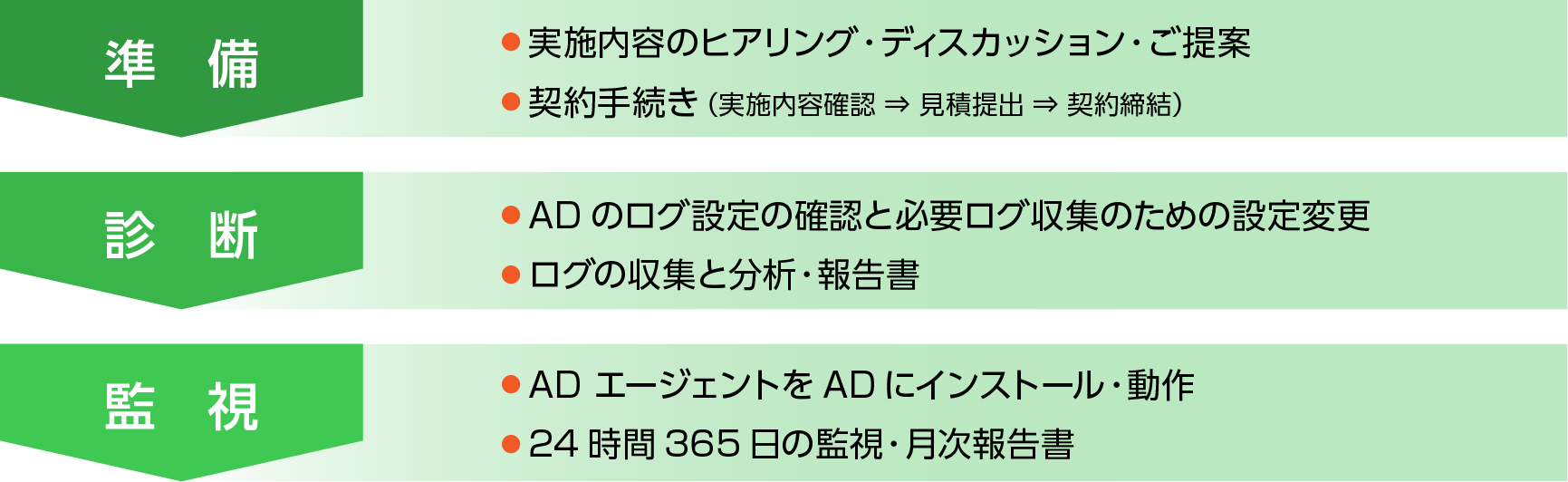
Flow until service introduction
Service overview
| Service item | Service details | remarks |
| Active Directory Spot diagnosis service |
Analyze and report on threats to Active Directory. | Provide an EVTX file and analyze whether the logon information with administrator privileges is legitimate. |
| Active Directory monitoring service |
Provides continuous analysis of threats to Active Directory and regular reports. | Continuously monitor and regularly report threats to AD. In the event of suspicious access or execution of PowerShell, we will promptly respond from the escalation remote. |
Inquiry/Document request
In charge of Macnica Security Service Co., Ltd.
- TEL:045-476-2010
- E-mail:sec-service@macnica.co.jp
Mon-Fri 8:45-17:30