Can XDR solve these problems?
At the request of Mr. Yoshikawa, who is in charge of field sales of security products, Mr. Yamada, a security expert and evangelist who works at Macnica, is in charge of information security at a parts manufacturer (pseudonym: Company A) that operates EDR and SIEM. I will be working with Mr. Otani. The purpose of the visit was to answer Mr. Otani's questions regarding XDR.
Character

| name | Kohei Yamada |
| age | 30's |
| sex | Male |
| Occupation | pre-sales engineer |
| Belonging department | Suspect |
| Outline | Active as a pre-sales engineer for security products. He also plays an evangelist role to raise awareness of the necessity of XDR inside and outside the company. |

| name | Rina Yoshikawa |
| age | 20's |
| sex | Woman |
| Occupation | sales |
| Belonging department | field sales |
| Outline | A new mid-career recruit assigned to Macnica 's security products sales team. In my previous job, I worked in IT product marketing and field sales for five years. However, I have no experience in sales of security products. |

| name | Hideki Ohtani |
| age | Forties |
| sex | Male |
| Occupation | Information Security Officer |
| Belonging department | Parts manufacturer with 2,000 employees (customer) |
| Outline | While planning the company's security policy, he began to become aware of the security management system. I'm not satisfied with how security can be strengthened by XDR, and I'm in trouble because I can't propose it to the company. |
What is the difference between EDR and XDR?

Mr. Yamada and Mr. Yoshikawa, I apologize for bothering you with your busy schedule.
No, it is our job to respond to customer inquiries.


Actually, the other day, Mr. Yoshikawa introduced me to a solution called "XDR (eXtended Detection & Response)," and I have some additional questions.

I'm sorry, I couldn't answer Mr. Otani's question.

No, no, it doesn't matter. On the contrary, it is helpful to have an expert come.
Ask me anything. Just to confirm again, you are already using "EDR (Endpoint Detection & Response)" and "SIEM (Security Information and Event Management)".


yeah, i use it. So I would like to know what will happen to EDR and SIEM with the introduction of XDR.
got it. First of all, regarding the relationship between EDR and XDR, I think it is easier to understand if XDR is the extension of the scope covered by EDR from Endpoint.


I see.
As you know, EDR is a great solution for threat detection and response. However, there are things that EDR can and cannot do, as shown in this diagram.

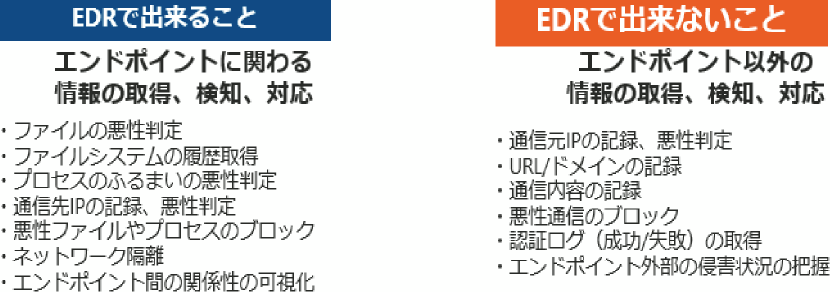
XDR means that XDR is the result of supplementing what EDR cannot do.


In other words, XDR is a mechanism that collects and analyzes logs not only from endpoints, but also from their surroundings, and enhances the ability to detect threats and investigate the causes of incidents.
exactly.

What is the difference between SIEM and XDR?

Do you collect logs from other security solutions that are not covered by EDR?
You are right. In XDR, security solutions such as EDR are called "sensors (or data sources)", and logs and alerts are captured from them.


Well, it's still similar to SIEM.
Would you say they are similar? SIEM and XDR are almost the same in terms of their goals. In addition, the core part of the mechanism for collecting and processing logs and alerts in XDR is the same as SIEM. For example, it looks like this figure.

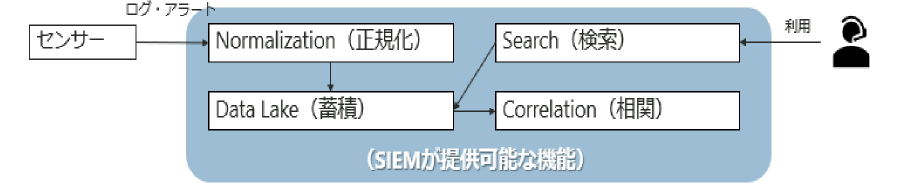

I see. Is the core mechanics the same as SIEM? To tell the truth, I already have a SIEM, but I haven't used it up. Are you saying that you are not fully responding to the alerts issued by the SIEM?
In that case, although logs and alerts are aggregated and accumulated for the time being and the alert status is visualized through the SIEM dashboard, investigation and analysis are conducted when an incident occurs, and the scope of impact and cause are quickly identified. Does that mean that it has not yet reached the target?


You're right.
XDR's solution is exactly the solution to that problem, and it can be said that XDR's existence value is there.


In short, you can effectively use SIEM as a security measure by introducing XDR. Since SIEM is the center of operations, it would be helpful if it could support the operation itself and make the work easier.
It will be easier. By using mature technology as XDR, you can visualize only really important alerts and threats and increase the speed of responding to those threats.


I see. In other words, XDR is not just for managing a wide range of security-related information and events, but is a solution for realizing prompt "Detection & Response."
You are right.

How can XDR reduce operation man-hours?

By the way, does XDR make operations easier? In other words, does it not only reduce the number of man-hours required to operate security measures, but also reduce the skills required for operation?
It is also possible.


If so, it would be really helpful for the Company. After all, in the case of the Company, the IT department has about 20 people, and only a few of them have appropriate knowledge and skills regarding security. To be honest, the reality is that there is not enough manpower to utilize EDR and SIEM in the current system. Also, last year, the person in charge retired, and the business temporarily fell into a very tight situation. For this reason, we felt that we needed to quickly create an environment in which even those who were not experts in security measures could properly operate security measures.
This situation is common not only in your company but also in many other companies. And that's why the Company 're doing our best to popularize XDR solutions.


So, I would like to ask you how you can reduce the number of operation man-hours and required skills by using the XDR solution.
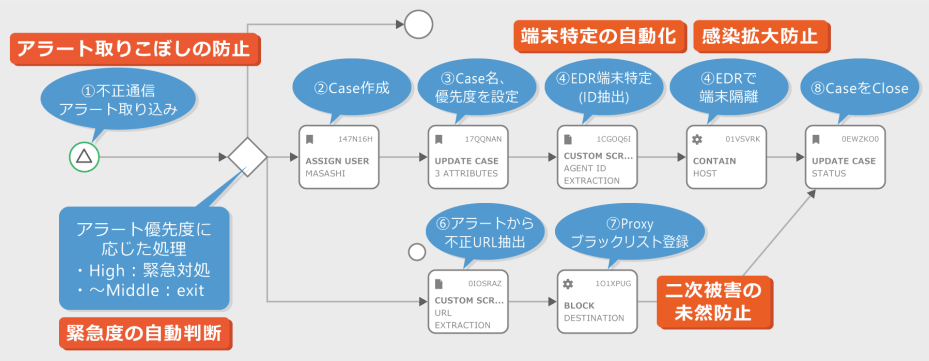
First, XDR uses SOAR to capture various alerts, including EDR, and automate necessary actions. In addition, incident response processing decisions can be made according to the urgency of the alert, and immediate responses such as identification of EDR infected terminals and network isolation can be automated.


I see. Do you mean that you can respond quickly without omission without human intervention, and that you can eliminate human dependence by setting judgment criteria?
In addition, for example, it is possible to prevent secondary damage by detecting malicious URLs from alerts and automatically registering them in the Proxy blacklist. These processes are summarized as shown in this figure.


This sounds good.
By properly defining security operations in this way and creating a mechanism as XDR, it is possible to improve the efficiency of operations.


Sounds good. With this, it seems that the risk of missing important alerts due to excessive logs and excessive alerts due to over-detection can be reduced.
You are right. In addition, while increasing the maturity of threat discovery and response, we can also increase the number of logs to be analyzed in stages and improve the accuracy of detection.

What is the right way to deploy XDR?

In the Company case, it took a lot of effort to introduce SIEM, but how much effort is required to introduce XDR? If the architecture is the same as SIEM, I imagine that it would take a lot of effort to introduce XDR.
Certainly, it usually takes a considerable amount of man-hours to introduce XDR. The design process, that is, the implementation process, is illustrated in this figure.

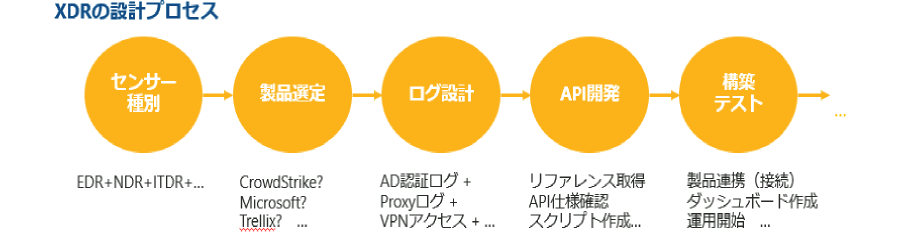

Hmm, you guessed it. If it takes this much time and effort, I wonder if the threshold for introduction is a little high for the Company.
The key here is how to choose a solution provider.


I mean?
First, consider that there are two broad types of XDR solutions.


two types?
Yes, two. One is a type of "closed XDR" that integrates tools from a single vendor. The other is "open XDR", which is based on the premise of linking with third-party products, providing APIs, and promoting alliances.


It is difficult for the Company to introduce “closed XDR”. Since we have already introduced EDR and SIEM, we cannot use the opportunity of introducing XDR to completely replace the environment with other products.
This is probably the case with many customers. Therefore, the key is how much you can reduce the effort required to introduce open XDR.


Does this mean that we should choose a provider based on the extent to which they can help us adopt open XDR?
You are right.


I see. So, based on Mr. Yoshikawa and Mr. Yamada's explanations, please bring us a proposal for an XDR solution.

of course. In order to make it easier to introduce open XDR, we are promoting the "XDR Lab" to verify XDR (introduction, testing, and operation) from the the Company 's perspective.
Oh, I knew about "XDR Lab" (laughs)


Of course.

I'm looking forward to your suggestions (laughs).
3 lessons learned
- What is the difference between EDR and XDR?
EDR is a solution for acquiring, detecting, and responding to endpoint information, while XDR is a mechanism that expands the coverage of EDR and makes it possible to do things that EDR alone cannot do. - What is the difference between SIEM and XDR?
XDR is a solution that encompasses SIEM, and XDR plays a role in making SIEM operations easier and increasing the ability of user organizations to detect and respond to threats. - What is the right way to deploy XDR?
It is to choose "open XDR" that is easy to cooperate with EDR and SIEM that have already been introduced, and to select a provider that supports its introduction.
Inquiry/Document request
In charge of Macnica XDR Co., Ltd.
- TEL:045-476-2010
- E-mail:XDR@macnica.co.jp
Weekdays: 9:00-17:00