Security Analytics

feature
- Three deployment options exist: appliance, software, and virtual appliance
- Add real-time index information to captured packets up to 10 Gbps
- Intuitive dashboard that can be customized freely
- Works with next-generation firewalls, Box, IPS, SIEM, and log management products from other vendors
- DPI function enables packet filtering by specifying protocol and file format
- Scalable storage for large-scale deployments
Introduction purpose
1. Incident Response
- Detect attacks and alert administrators
- Investigate the extent of impact
- Extract malware samples
- Judgment by reputation
- Identify information leaked through targeted attacks and unauthorized access
2. Internal audit / compliance
- Audit inappropriate site browsing and e-mail/file sending/receiving
- Extract statistics for reporting
3. Network management
- Network visualization
- Detect and warn of abnormal behavior
- Analyze communication failure bottlenecks
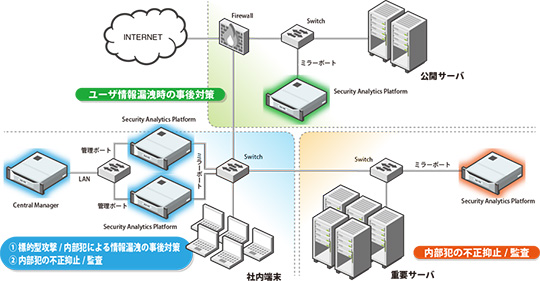
Network configuration diagram
screen image
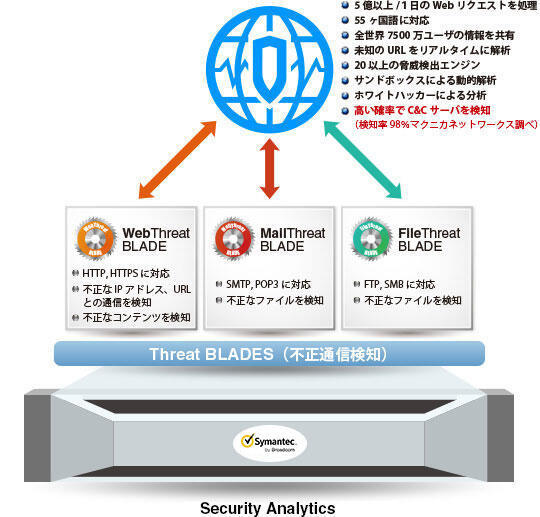
Threat Blades (unauthorized communication detection function)
Detect unauthorized communications by leveraging Broadcom intelligence.
Global Intelligence Network (threat information database)