
Okta
Octa
Brief description
Explain SSO.
- What is SSO (Single Sign On)?
- Authentication method for realizing SSO
- SAML
- Sp initiated and IdP initiated
- Okta Integration Network (OIN)
- Okta portal screen
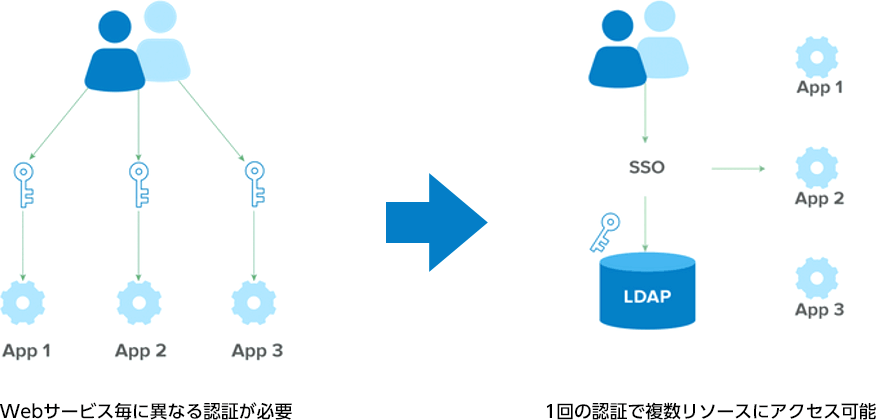
What is SSO (Single Sign On)?
- This function enables authentication for multiple web services with only one set of ID/Password.
- In particular, if Okta is introduced, SSO can be achieved even between service providers with different deployment environments such as cloud, on-premises, and mobile applications.
Authentication method for realizing SSO
- SAML
Standard protocol, supported by many products. - WS-Federation
It is often used in Microsoft products. Similar behavior to SAML. - Secure Web Authentication (SWA)
An authentication scheme created by Okta to provide SSO for applications that do not support SAML. Install the Okta plugin in the user's browser and let the plugin fill in the credentials on your behalf. - Open ID Connect
A standard mechanism for next-generation authentication and federated identity systems.
SAML
SAML: a protocol for services to delegate authentication to the outside world
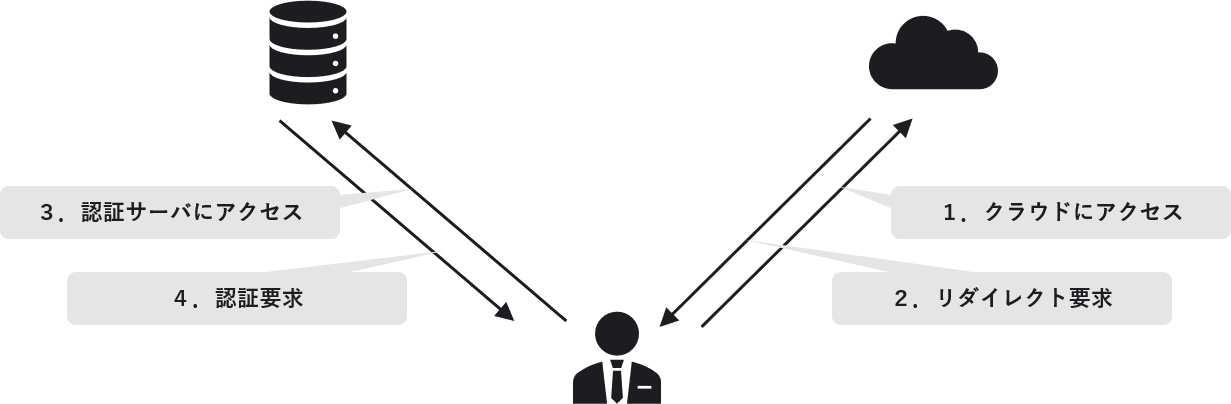
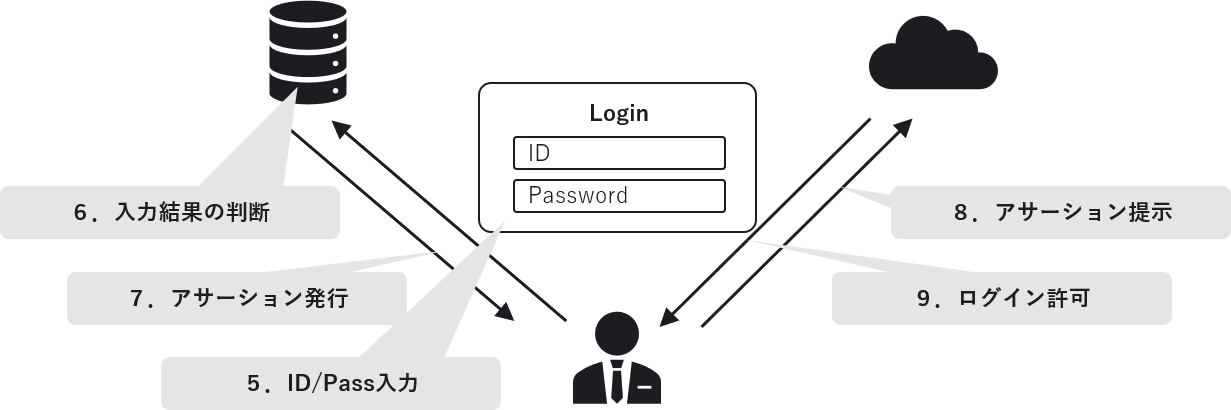
Sp initiated and IdP initiated
Differences in authentication order
- Sp initiated: format starting with Sp
-
- Access Box → Enter your email address → Transition to the IdP screen
- Access Microsoft 365 → Enter UPN → Transition to IdP screen
- IdP initiated: format starting with IdP
-
- Okta Portal
* Depending on the specifications of the SP, only one of them may be available.
Okta Integration Network (OIN)
- Okta comes pre-configured with a set of configurations for major web applications.
* More than 6,000 sites (1,500 visible with evaluation license) - Simply select any application from a catalog (list) called OIN
Single Sign-On linkage is possible. - WEB services that are not on OIN can also be linked by creating new ones yourself.
(Own web application, etc.)
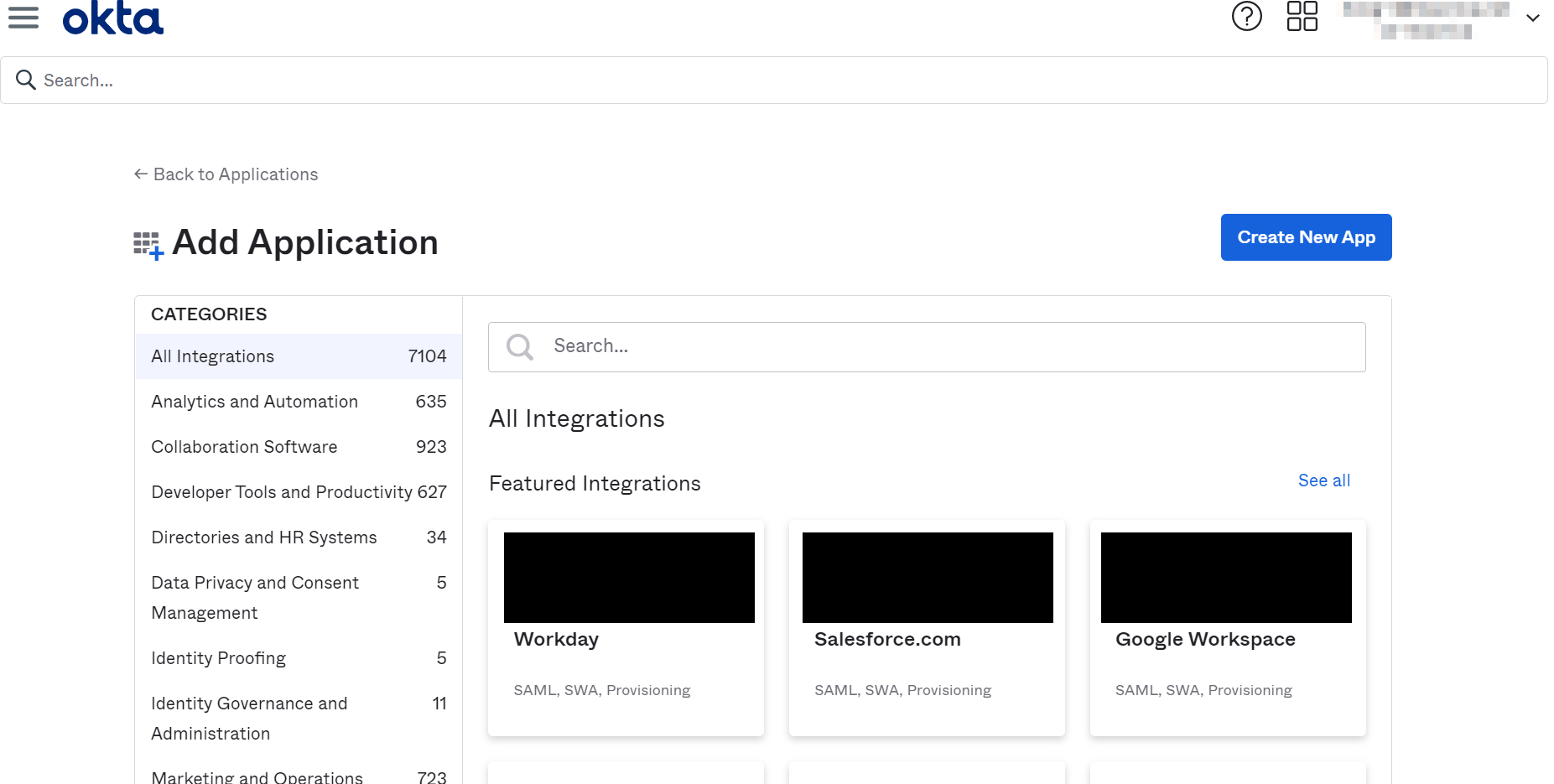
Just find the application in the search filter and press the Add button
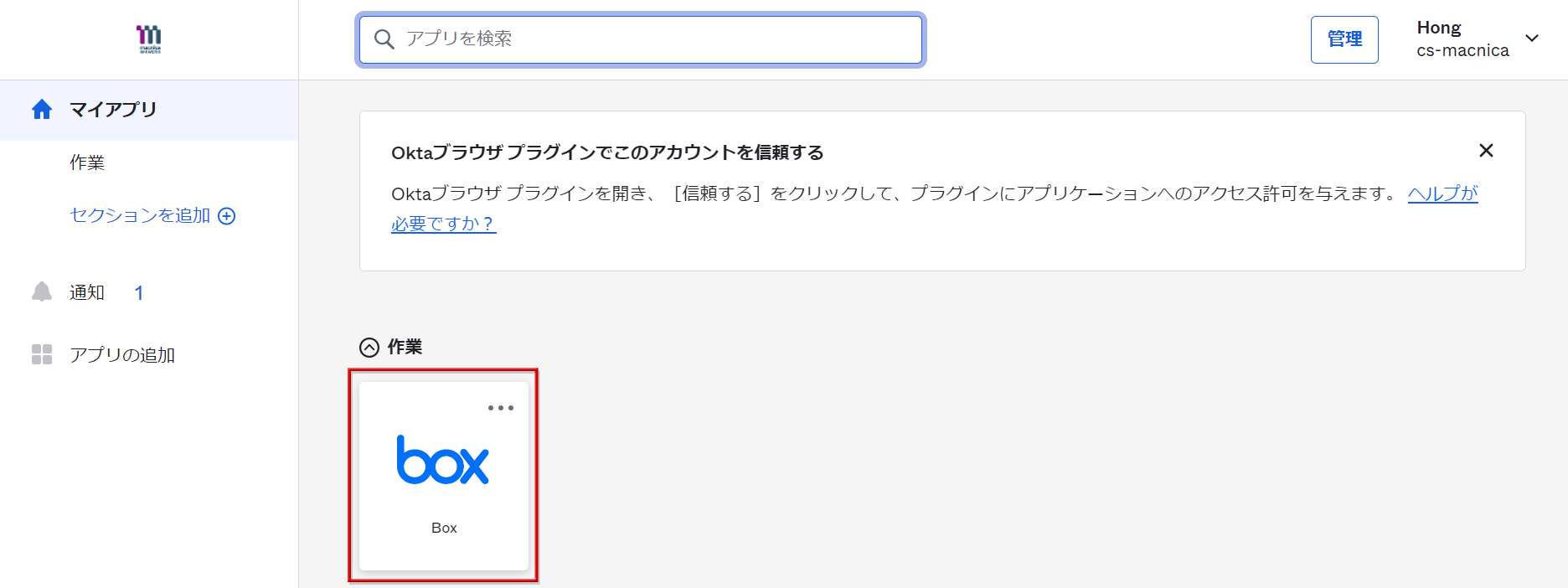
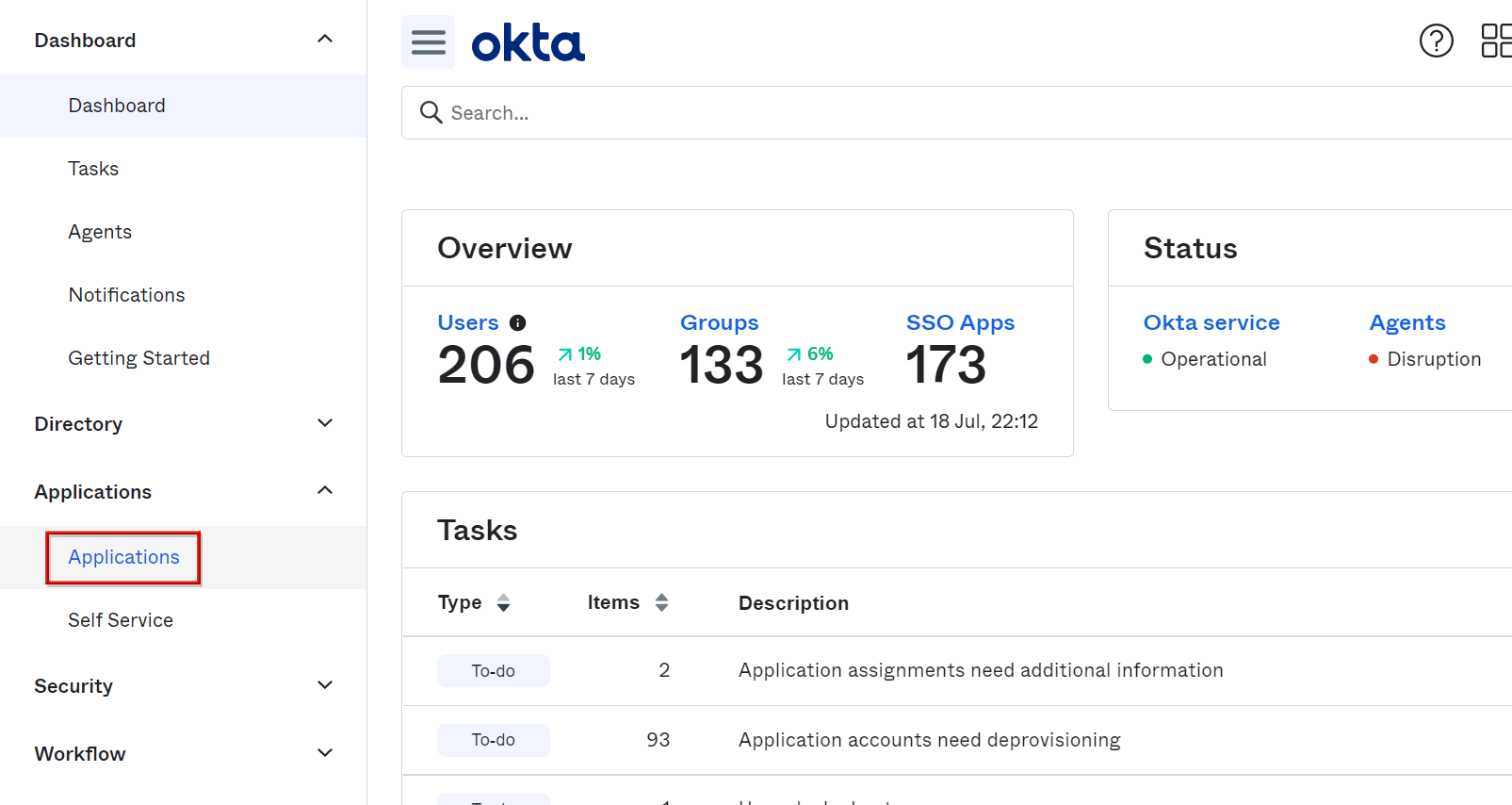
Okta portal screen
Web portal
There is a portal screen for Okta users, and you can access each resource by clicking the service icon. (Folders can also be divided)
Add OIN Application
This section explains how to create a SAML application using OIN.
- Add OIN Application
- Refer to the OIN manual and make additional settings
- User assignment
- User assignment [Supplement]
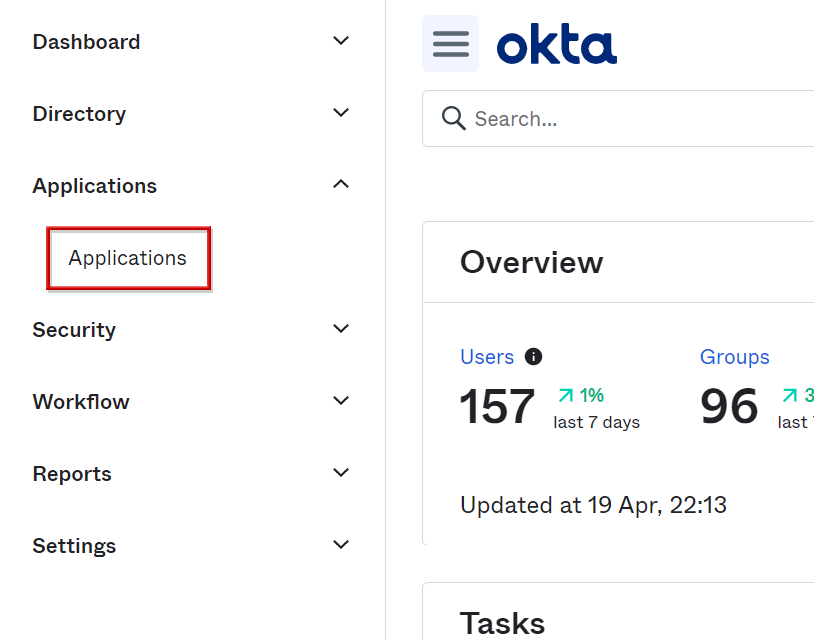
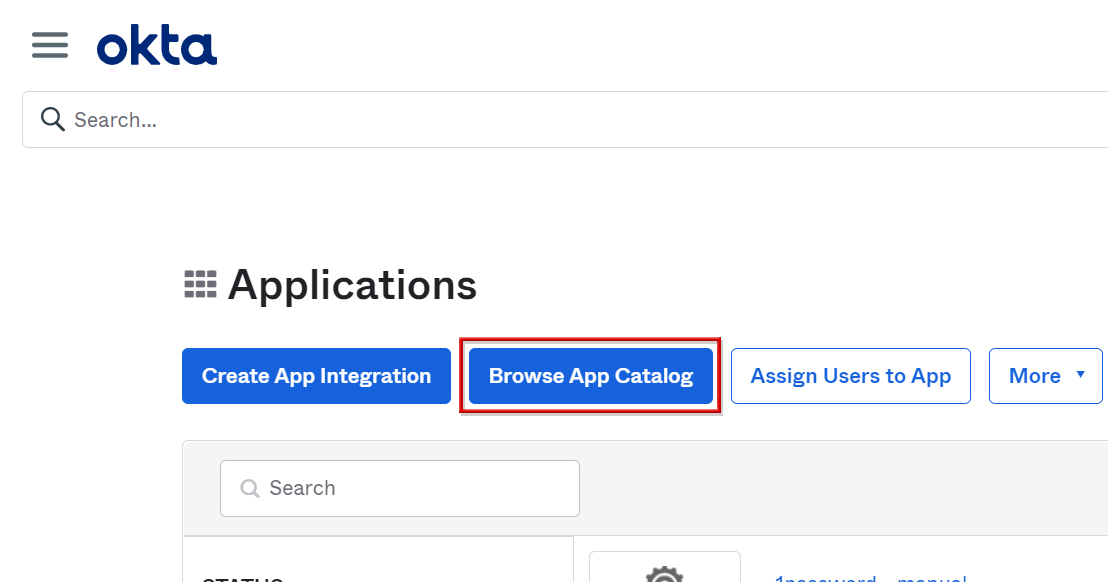
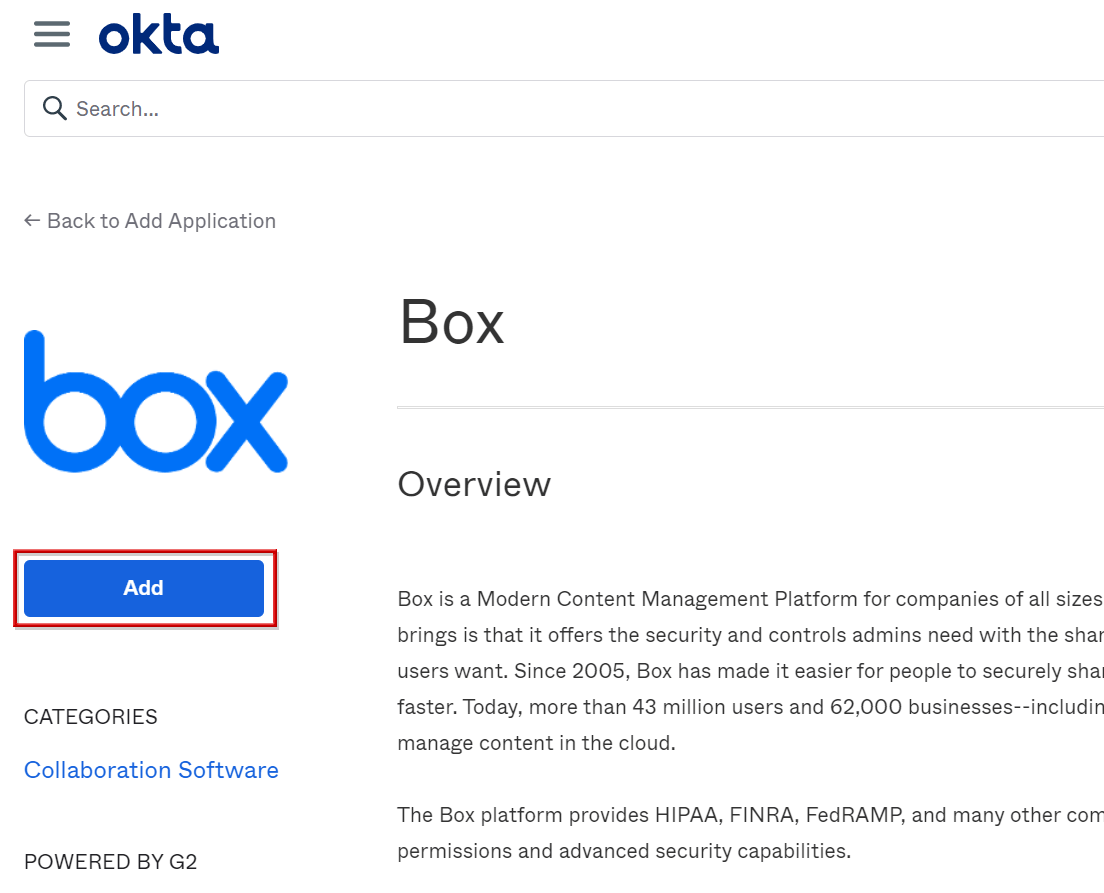
Add OIN Application
- Go to Applications > Applications screen
- Click Browse App Catalog
- Enter part of the application name you want to create in the search form and select from the displayed search results
*In this procedure, Box is selected as an example.
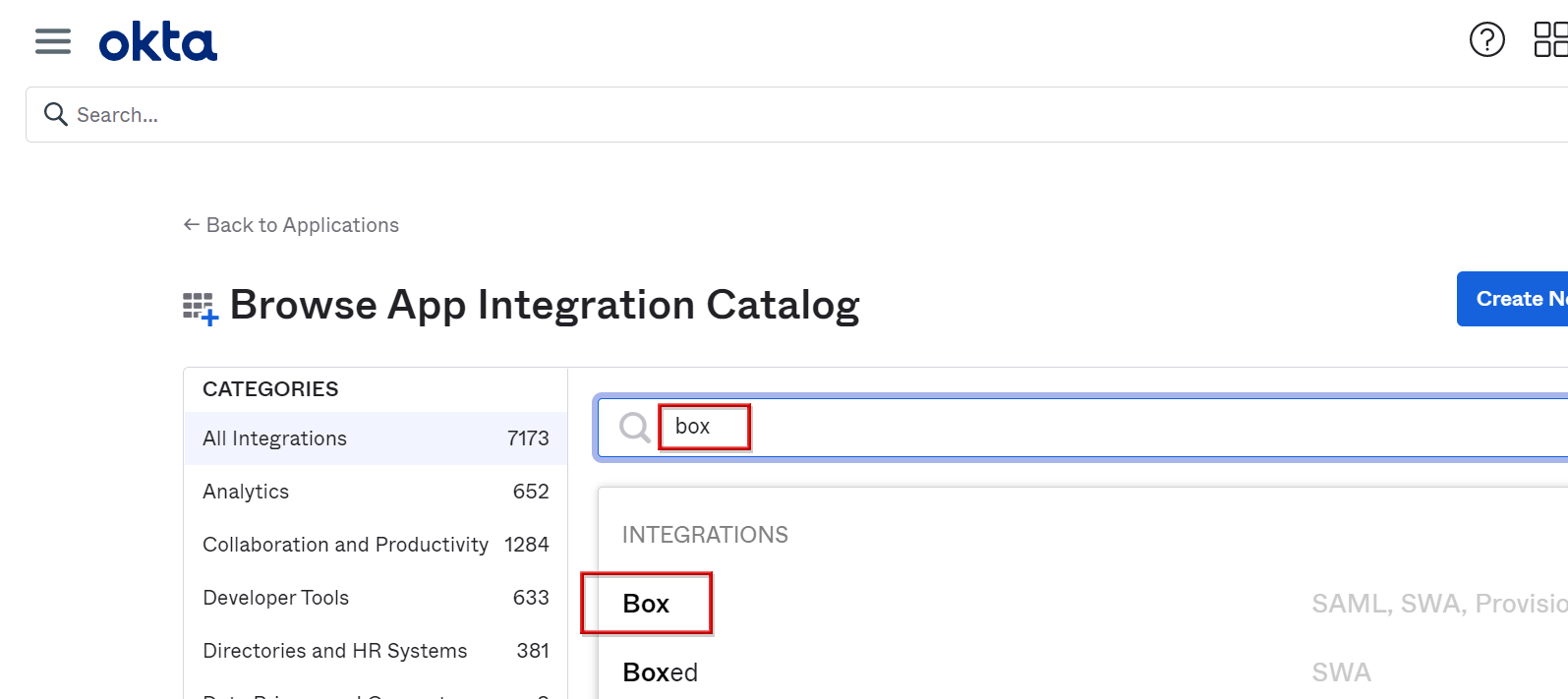
- Click Add
- Enter any app name in Application label, then click Done
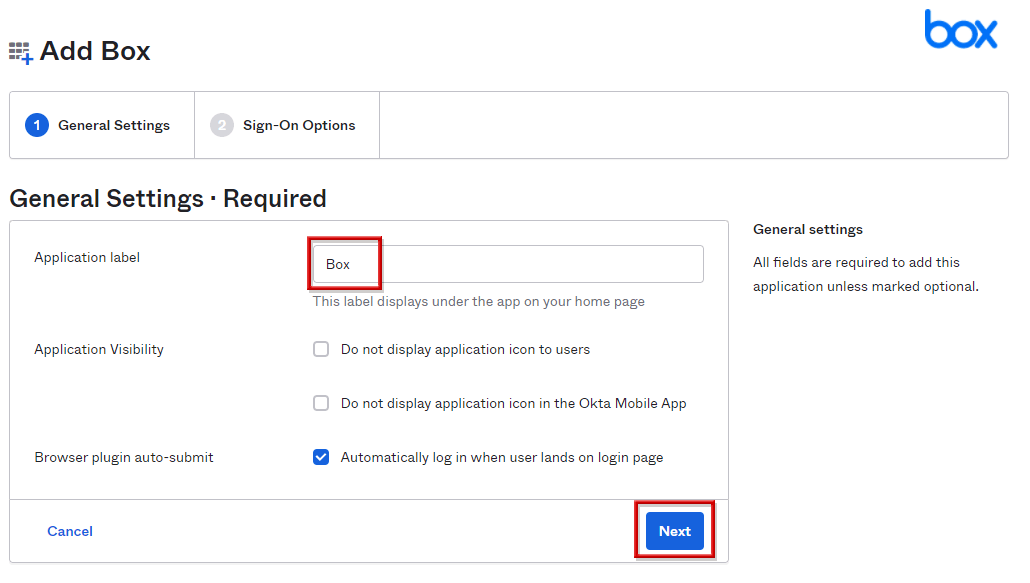
* The setting screen may differ depending on the OIN template.
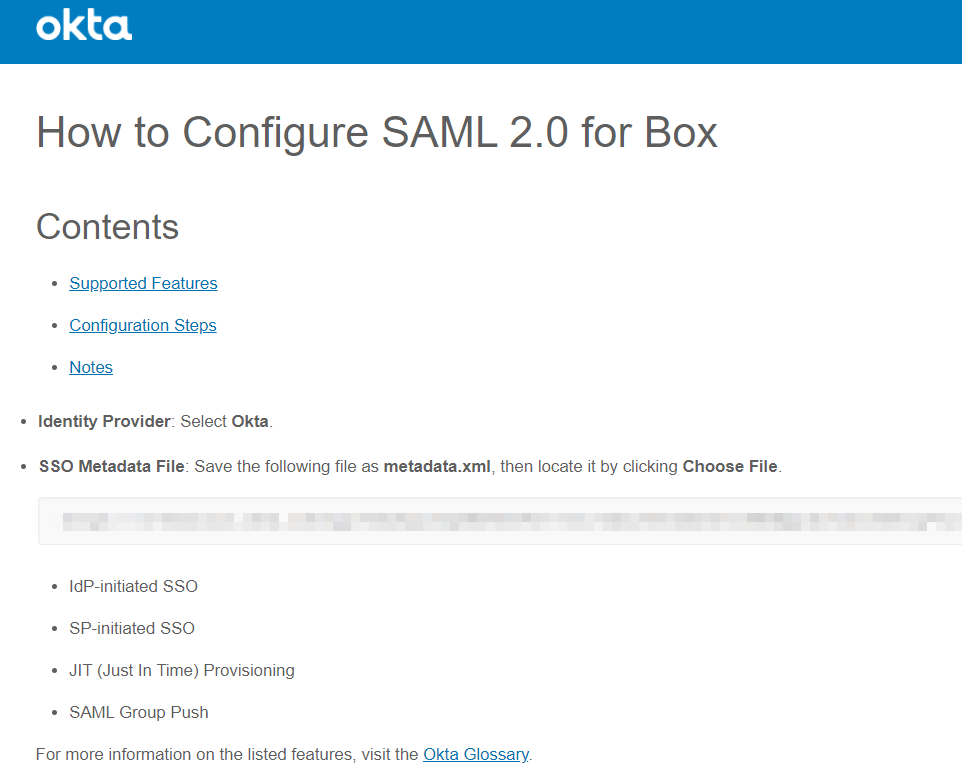
Refer to the OIN manual and make additional settings
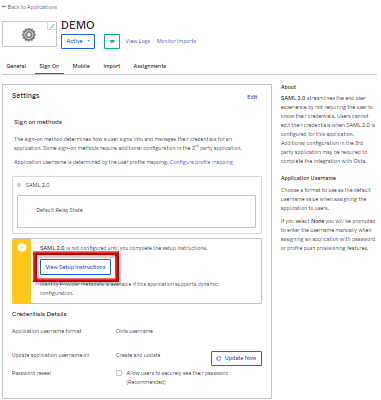
- Click the Sign On tab, and in Settings View Setup Instructions click the button
(Transition to the OIN manual page shown below)
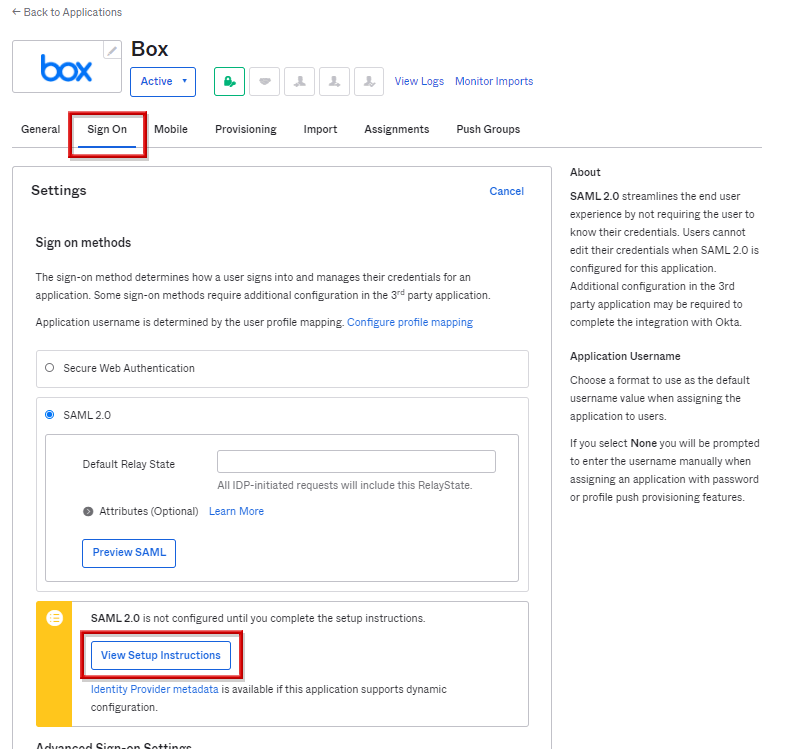
- Since the procedure manual is displayed, confirm that the customer-specific character string including the Okta tenant name etc. to be entered on the SP (application) side is displayed, and proceed with the setting of cooperation with the SP.
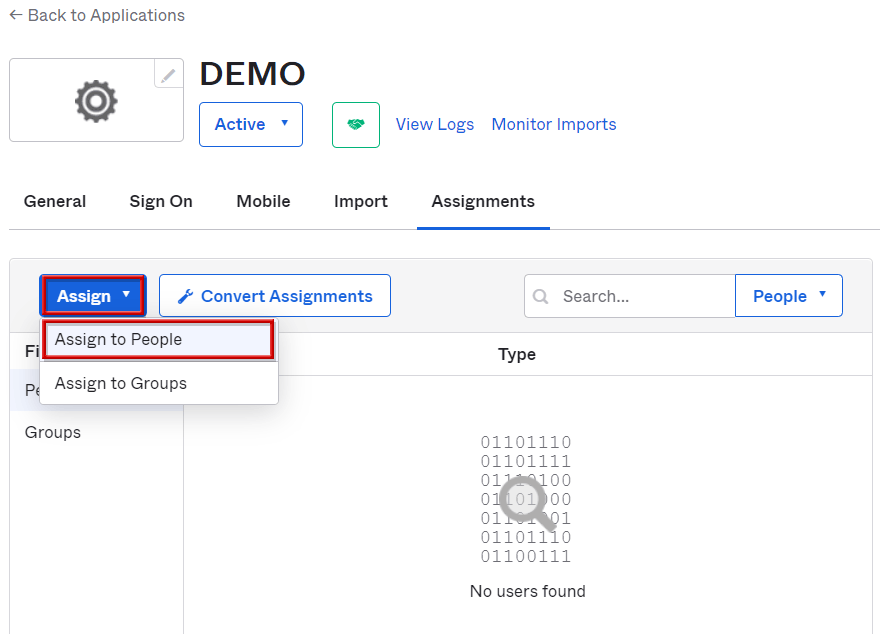
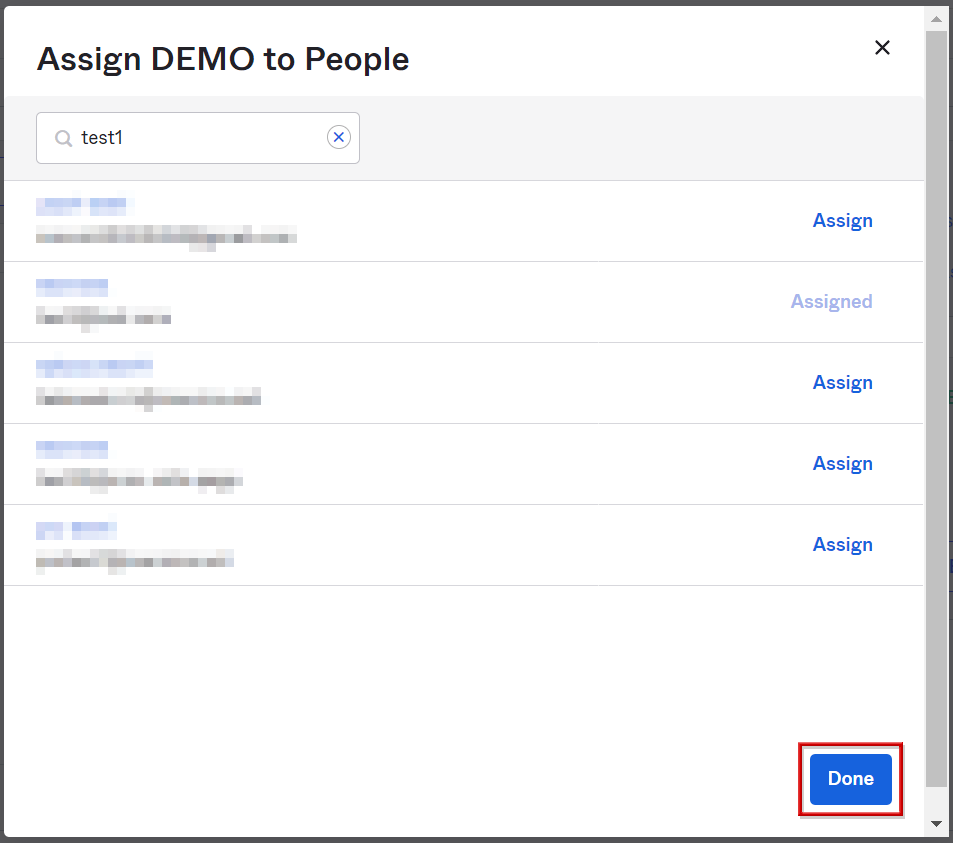
User assignment
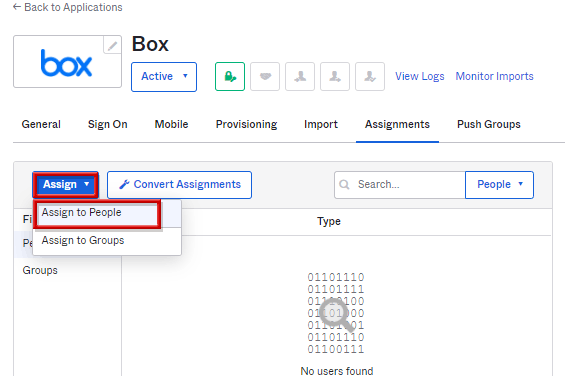
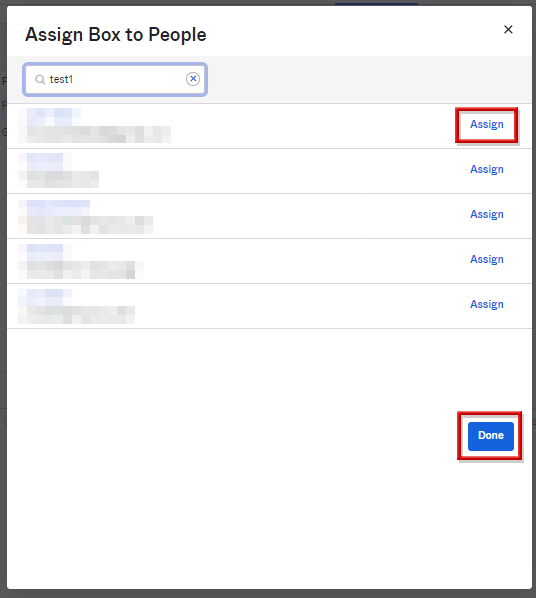
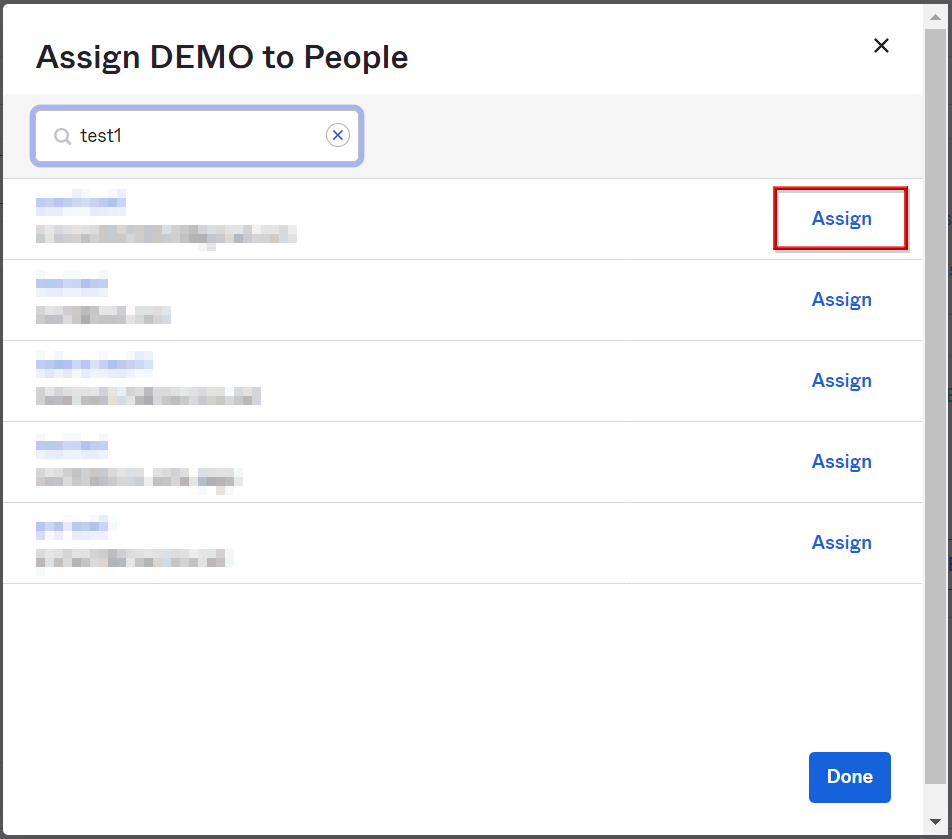
- On the Assignments tab, click Assign, then click Assign to People
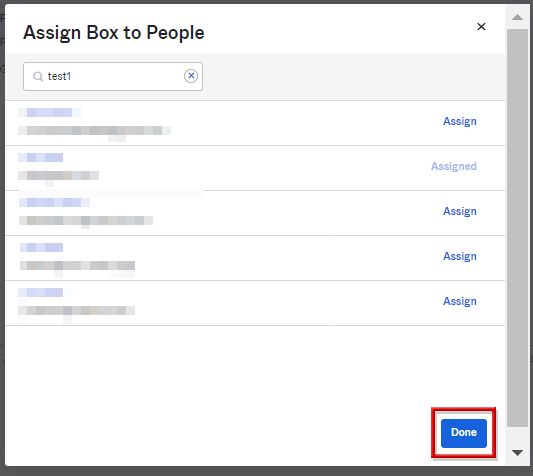
- Select users to access this application with Assign
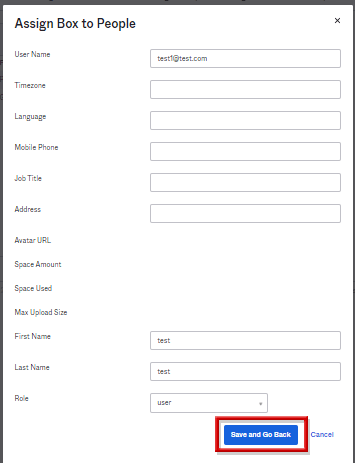
- Enter the account name used to access this application in the User Name field. Enter other necessary items and click Save and Go Back *If there is no problem with the default, leave it as it is.
- Click Done to complete user assignment
User assignment [Supplement]
The icon of the previous application will be displayed on the assigned user's portal screen.
After setting up the linkage, click here to start the SSO connection.
![User assignment [Supplement]](/business/security/manufacturers/okta/image/okta_guide_saml_sso17.png)
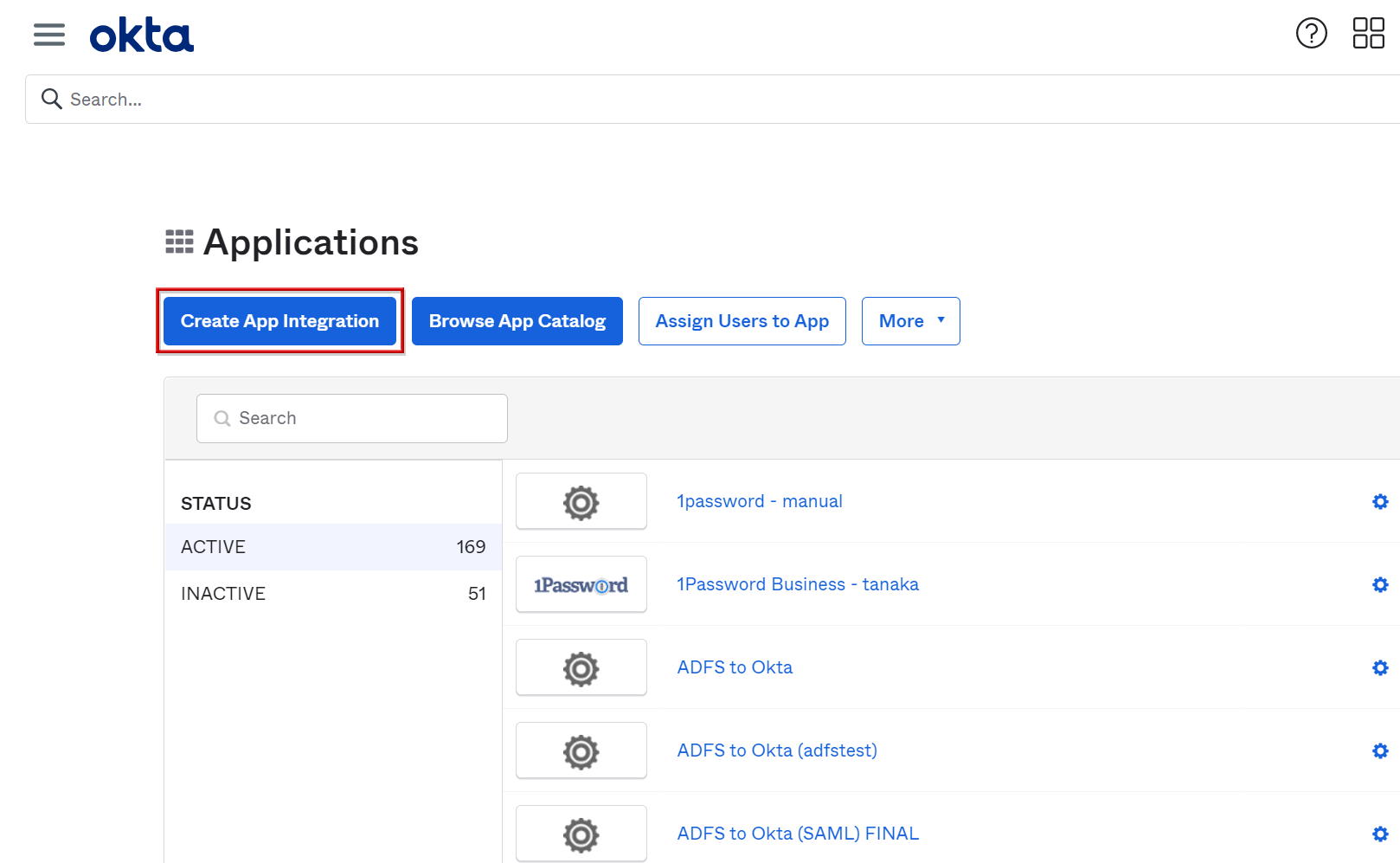
Adding applications without OIN
Describes the procedure for creating a SAML application without OIN.
Adding applications without OIN
- Transition to Applications > Applications screen
- Click Create App Integration
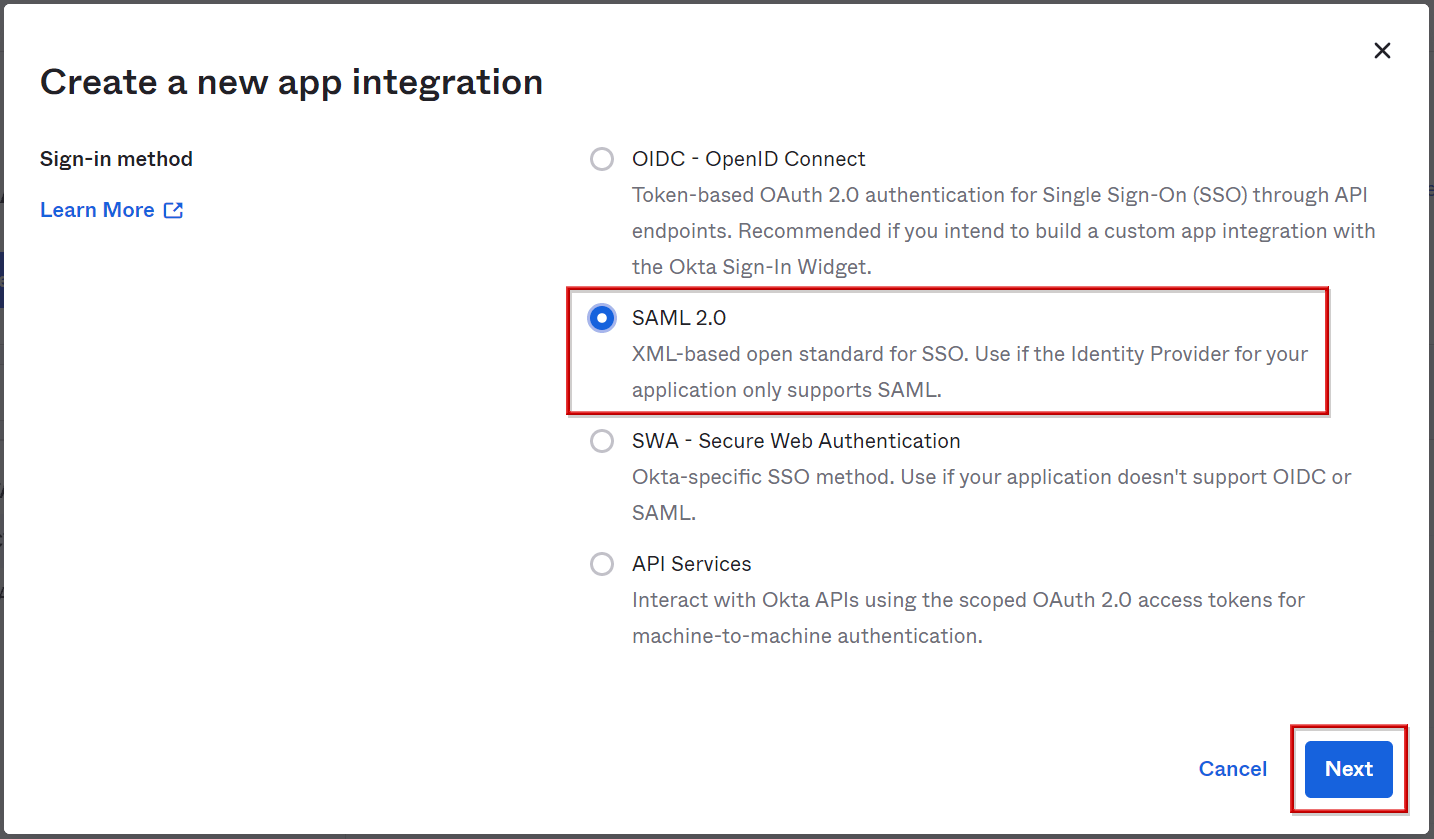
- Select SAML2.0 and click Next
*For applications that support SAML2.0
- Enter the application name and click Next
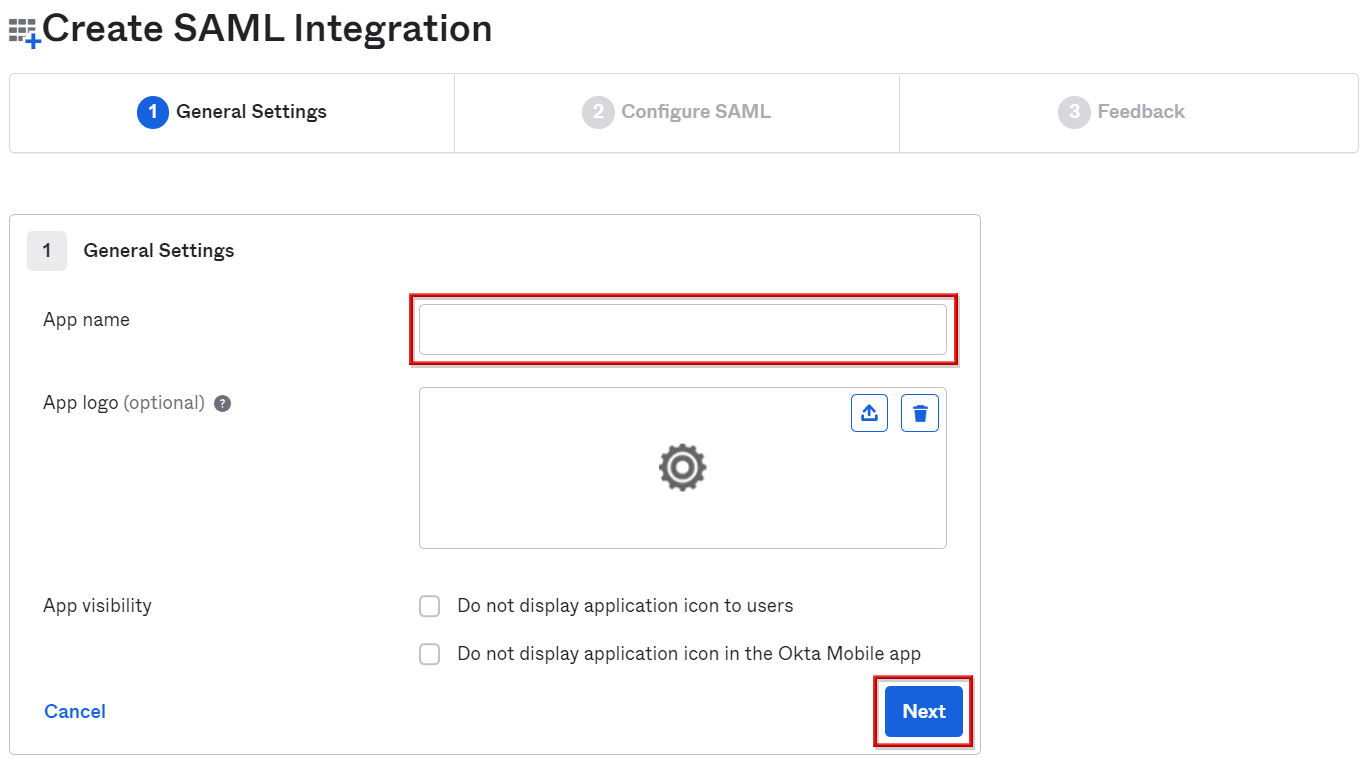
*There is no problem with the default logo, but it is recommended to set it to make it easier to identify.
- Enter application login URL and Entity ID
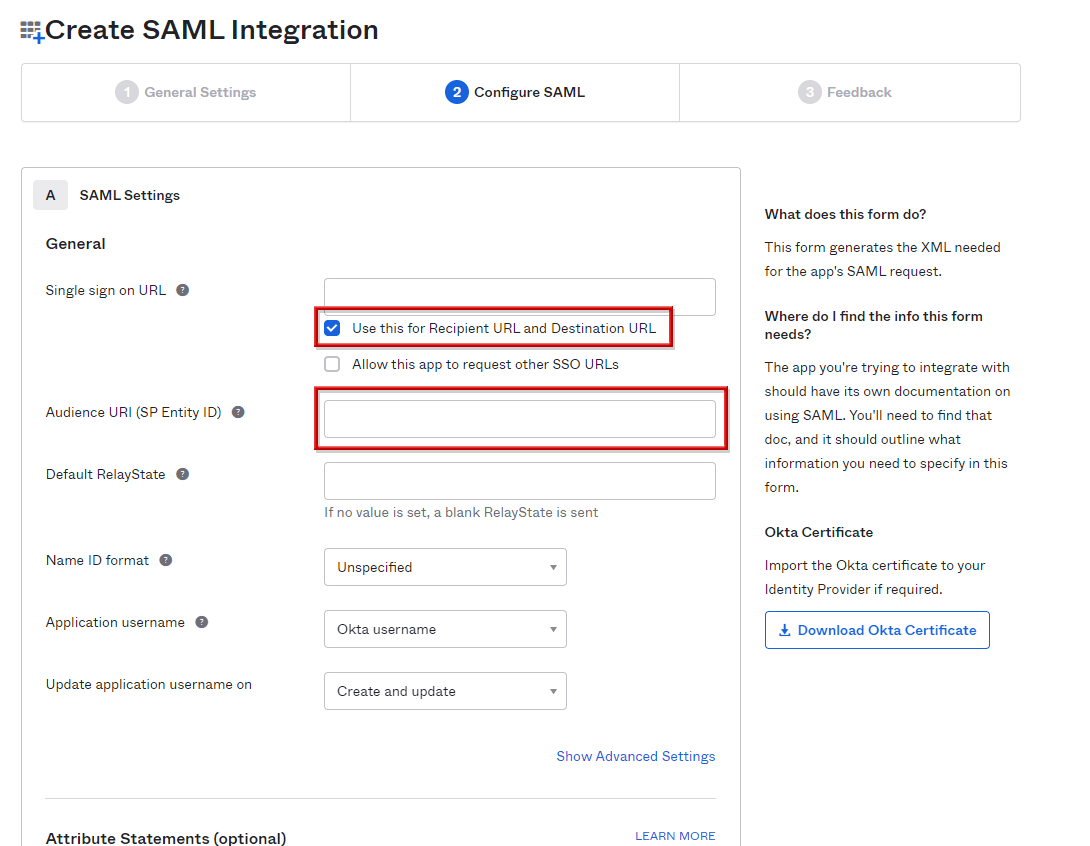
- Go to the bottom of the page and click Next
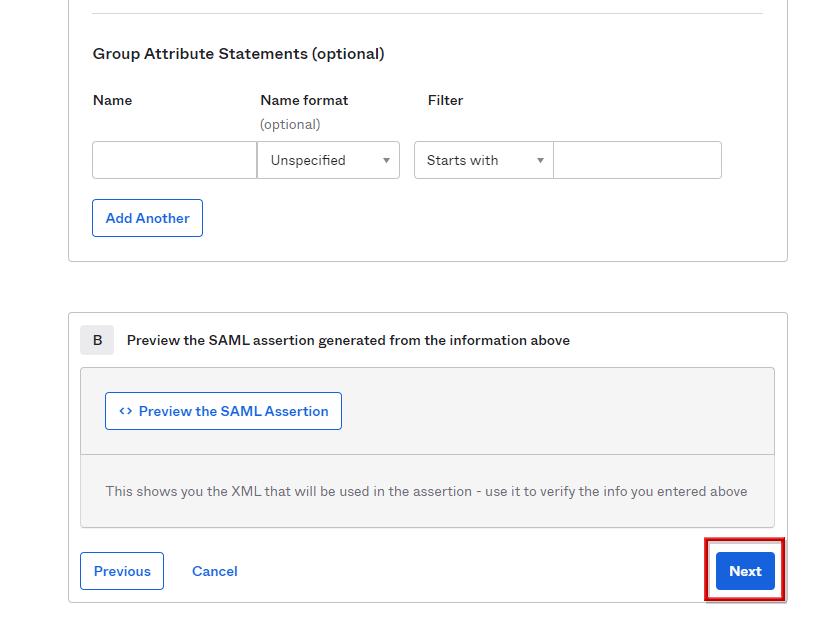
- Select I'm an Okta customer adding an internal app and click Finish
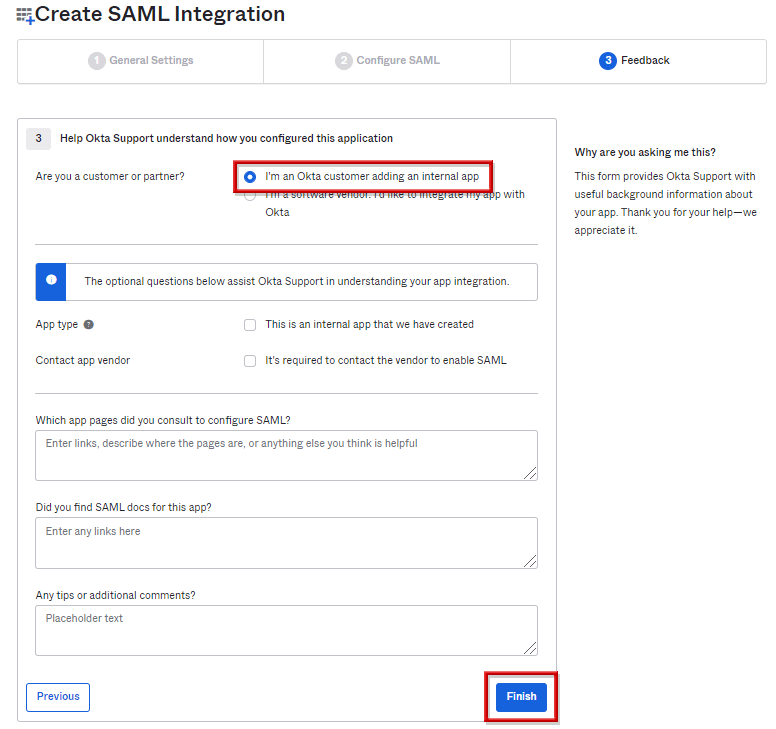
Acquisition of setting values to SAML application
- Click View Setup instructions on the Sign On tab
- Since the SSO URL and certificate on the Okta side are displayed, setting is completed by reflecting it on the application side
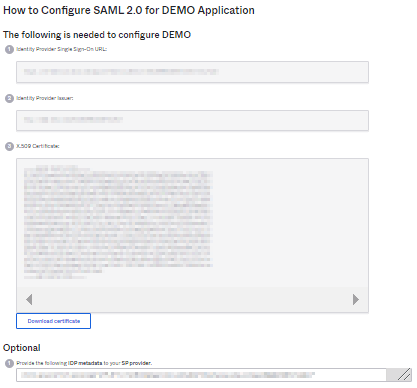
[Supplement] Acquisition of setting values for SAML application (metadata)
- Metadata can be obtained from Identity Provider metadata on the Sign On tab
![[Supplement] Acquisition of setting values for SAML application (metadata)](/business/security/manufacturers/okta/image/okta_guide_saml_sso27.png)
- Metadata can be saved in the target file and this data can be reflected in the application
![[Supplement] Acquisition of setting values for SAML application (metadata)](/business/security/manufacturers/okta/image/okta_guide_saml_sso28.png)
User assignment
- On the Assignments tab, click Assign, then click Assign to People.
- Select the users to access this application in Assign.
- Enter the account name to be used when accessing with this application in User Name. Then click Save and Go Back
*If there is no problem with the default, leave it as it is.
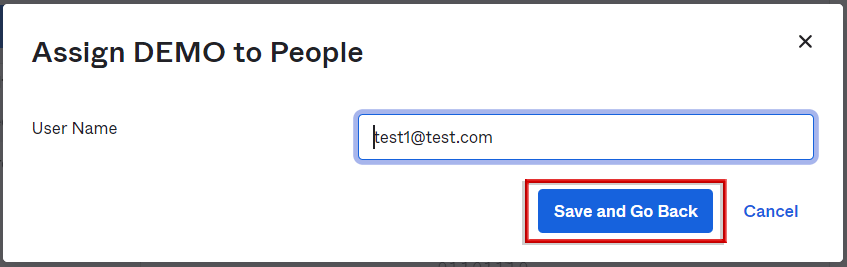
- Click Done to complete user assignment
Inquiry/Document request
In charge of Macnica Okta Co., Ltd.
- TEL:045-476-2010
- E-mail:okta@macnica.co.jp
Weekdays: 9:00-17:00